- Jan 04, 2024
- 6 min read
Customer Reverification: What It Is and Why It Matters. Complete Guide for 2024
Learn about what reverification is and why it’s crucial for any business.
70% of fraud occurs after the initial KYC stage. This shows that one-time verification is no longer enough in the fight against fraud. So, let's dive into customer reverification, its key components, best practices, and future trends.
What is reverification?
Reverification is the process of periodically reconfirming the accuracy of customer information and risk profiles as part of ongoing monitoring and Customer Due Diligence (CDD)—two key components of a risk-based approach to regulatory compliance.
The goal of reverification is to ensure that businesses have up-to-date information about their customers and can identify any changes in their risk profile over time. This helps organizations comply with regulatory requirements and mitigate all potential risks associated with their customers.
The reverification process may include the following checks:
- Identity verification. Confirming the customer's identity through documents like passports, driver's licenses, or other official identification.
- Address verification. Confirming the customer’s permanent address and residency through documentation such as recently-issued utility bills and bank statements.
- Contact information. Verifying and updating the customer's contact details, including addresses, phone numbers, and email addresses.
- Business information. For corporate clients, ensuring that the business information remains accurate, including changes in ownership, structure, or key personnel.
- Source of funds. Reassessing the source of funds or wealth of the customer to ensure they align with the declared and expected financial activities.
- Ongoing monitoring. Rechecking the customer's transaction history to prevent money laundering and fraud-related risks, if conditions change.
- Risk assessment. Re-evaluating the customer's risk profile based on the collected information and adjusting risk categorization accordingly.
Importance of reverification
Customer reverification is important because it ensures that customer information remains accurate and up-to-date over time. As changes in identity, contact details, or financial information occur, regular reverification helps companies adapt to these changes.
By periodically confirming customer data, organizations can enhance their ability to detect and prevent fraud, money laundering, terrorist financing and other illicit activity. Additionally, reverification supports compliance with regulatory requirements, as authorities often mandate continuous monitoring and due diligence to mitigate financial risks. It also allows businesses to understand their customers' risk profiles, facilitating effective risk management strategies.
Let’s dive into the details of why verification is crucial.
Ensuring data integrity
Reverification plays a crucial role in ensuring data integrity by reconfirming and updating customer information from time to time. This process helps maintain the accuracy of data over time, contributing to a reliable and trustworthy database for effective decision-making and compliance efforts.
Enhancing security measures
Reverification strengthens security measures, enabling businesses to identify and respond to potential security risks or fraud in a timely manner. This approach enhances overall security protocols, reducing the likelihood of unauthorized access, account takeovers, multi-accounting, financial crimes, and other threats.
Compliance with regulations
Reverification ensures that customer information remains accurate and aligns with evolving regulations. Many regulations mandate continuous monitoring and due diligence to detect and prevent illegal activities, such as money laundering. By regularly reconfirming customer data, organizations remain compliant and reduce the risk of penalties or legal consequences.
Monitoring account activity
Reverification helps financial institutions monitor customer account activity for any suspicious or unusual transactions. Unexplained withdrawals, transfers, or changes in spending patterns can be indicators of fraudulent activity or identity theft. By closely monitoring account transactions, institutions can identify and take appropriate action to prevent further harm to the customer.
Suggested read: The Complete Guide to Transaction Monitoring
Suggested read: Cryptocurrency Transaction Monitoring: How It Works in 2023
Educating customers
Reverifying customer identities also provides an opportunity to educate customers about protecting their personal information. This includes advising them on strong password usage, avoiding phishing scams, regularly monitoring their financial accounts, and reporting any suspicious activity promptly.
Customer relationship management
Regular reverification of customers enables financial institutions to maintain accurate and up-to-date customer information, aiding in effective customer relationship management and providing personalized services to customers based on their needs and risk profiles.
Enhanced Due Diligence (EDD)
The reverification process allows regulated entities to update high-risk customers subject to EDD. This helps in assessing the potential risks associated with the customer's transactions and activities.
Key components of the reverification process
The key components of the customer reverification process include identity confirmation, credential management, analysis of customer activity, biometric verification, and more. Let’s dive into the details:
Identity confirmation
During reverification, organizations review and confirm the accuracy of customer identity information to ensure it remains current. This may involve validating official identification documents, checking personal details, and ensuring that the customer's identity aligns with the information on record. The goal is to maintain the integrity of customer data and comply with regulatory requirements by periodically confirming the accuracy of identity information.
Authentication protocols
Reverification may involve the use of various authentication protocols (e.g. Challenge-Handshake Authentication Protocol, etc.) depending on the specific requirements and security measures implemented by an organization.
Credential management
Reverification helps users update their credentials, ensuring account security. Here are key aspects of credential management during the reverification process:
- Password and password policy updates
- Credential storage update
- Multi-Factor Authentication (MFA) settings
- Access control
- User authentication protocols
- Credential expiry
Two-Factor Authentication (2FA)
Two-Factor Authentication (2FA) can be part of the reverification process. Integrating 2FA into reverification adds an extra layer of security by requiring users to provide two distinct forms of identification to confirm their identity. Here's how 2FA can be incorporated into the reverification workflow:
- Initial authentication. Users start the reverification process by providing their standard credentials, typically a combination of a username and password.
- Second factor of authentication. After the initial authentication, the system prompts users to provide a second factor of authentication. This could be a temporary code sent to their mobile device, the use of a biometric identifier (such as a fingerprint or facial recognition), or another authentication method.
- Identity confirmation. The successful completion of both the initial authentication and the 2FA challenge confirms the user's identity during the reverification process.
- Adaptive 2FA. Some systems implement adaptive 2FA, where the strength of authentication is adjusted based on contextual factors and risk assessments. For example, if a user is attempting to log in from an unusual location, additional 2FA challenges may be triggered.
Biometric reverification
Biometric reverification refers to the process of confirming and validating the identity of individuals by utilizing their unique biological traits. In the context of reverification, biometric data is used as an additional layer of authentication to ensure that individuals are who they claim to be.
The steps involved in biometric reverification typically include:
- Initial authentication. Users begin the reverification process by providing standard authentication credentials, such as a username and password.
- Biometric capture. Following the initial authentication, users are prompted to provide a biometric sample, which is then captured by a biometric sensor or device.
- Biometric matching. The captured biometric data is compared with the previously stored biometric template associated with the user's account.
- Identity confirmation. A successful match of the biometric data, combined with the initial authentication, confirms the user's identity during the reverification process.
Reverification in the context of security
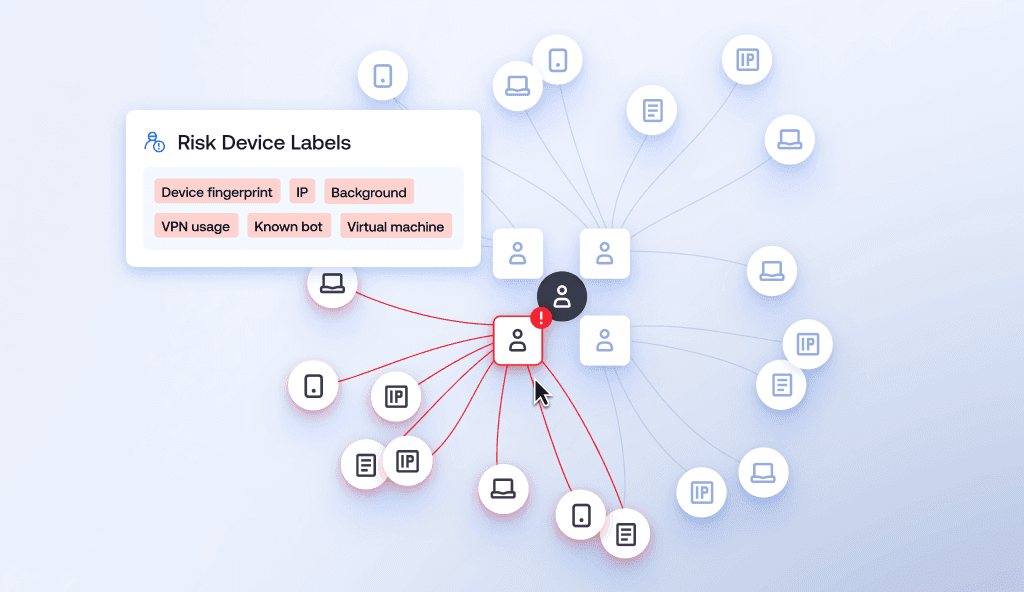
Fraud and identity theft protection measures
Incorporating reverification into risk management and fraud prevention strategies enables the following:
- Early intervention: Timely reverification allows companies to identify and respond to suspicious changes in account information promptly. Unauthorized changes, such as updated contact details or address, can signal an attempted account takeover or identity theft. By catching such changes early, institutions can intervene to prevent further harm to the customer and mitigate potential losses.
- Mitigation of stolen identities: Reverification helps detect when unauthorized individuals may have gained access to an account.
- Enhanced security with MFA: Integrating reverification with multifactor authentication methods, such as 2FA or biometric verification, adds an extra layer of security, making it harder for fraudsters to gain unauthorized access.
- Real-time monitoring: Real-time and ongoing monitoring of user activities can include reverification.. Unusual patterns or high-risk behaviors can trigger alerts, allowing organizations to investigate potential fraudulent activities promptly.
- Compliance with regulations: Many industries are subject to regulations that mandate continuous monitoring and due diligence. Reverification ensures compliance with these regulations, contributing to effective fraud prevention measures.
Access control updates
Access control update is the process of modifying the permissions and privileges granted to individuals (or entities) within an organization. This involves reviewing and, when needed, changing the level of access which users have to certain resources, data, or functionalities based on their roles, or changes in organizational requirements.
Reverification is crucial for access control updates as it allows organizations to recheck the accuracy of user information, ensuring that access rights align with current roles and responsibilities.
Use cases
Below are the most widespread examples when reverification is needed:
- When key account information is changed
- When documents expire
- When a user initiates a high-risk action, such as transferring a significant sum of money to another account
- Account reactivation
- Logins from suspicious IPs or locations
- Account maintenance
- Security protocols in the aftermath of a data breach or fraud incident
- Regulatory compliance.
Future trends
The future trends of reverification are likely to involve:
- Increased integration of artificial intelligence and machine learning for more robust risk assessment and anomaly detection
- Biometric verification methods
- Behavioral analytics
- Decentralized identity solutions where individuals have more control over their personal information
Suggested read: Why Behavioral Analytics is Key to Fraud Detection Today
FAQ
-
How does reverification affect user experience?
Reverification can have both positive and negative impacts on the user experience. Reverification enhances security and protects against unauthorized access, however, additional authentication steps can be inconvenient for clients.
-
Which industries benefit the most from reverification?
Industries with strict regulatory requirements, such as finance, banking, and healthcare, can benefit the most from reverification as it helps them comply with regulations, enhance security, and mitigate the risk of financial crimes or unauthorized access to sensitive information.
-
Are there risks associated with reverification?
The risks include user frustration due to additional authentication steps and the possibility of false positives in anomaly detection, leading to legitimate users being flagged for further scrutiny.
-
Can reverification be done remotely? If so, how?
Yes, reverification can be conducted remotely using various methods, including online identity verification, video calls for visual confirmation, and secure authentication processes, such as MFA or biometric verification, allowing organizations to confirm and update user information without requiring physical presence.
Relevant articles
- Article
- Apr 22, 2026
- 5 min read

- Article
- 2 weeks ago
- 12 min read
Learn how device intelligence assesses device risk in real time using technical signals and device fingerprinting—without disrupting the customer exp…
What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.