- Mar 23, 2026
- 20 min read
Transaction Monitoring in AML: Ultimate Guide For 2026
AML transaction monitoring in 2026: How it works, key typologies, regulations, and how to choose the right system.

Monitoring financial transactions and user activities is an important task for all companies for different reasons, mostly to avoid financial crime. For both regulated businesses, such as financial institutions and virtual asset service providers (VASPs), and non-regulated ones, it serves as a critical tool for managing fraud and financial crime risks. And for regulated ones, AML transaction monitoring is also a key regulatory requirement.
Getting transaction monitoring wrong can be very costly. Regulators can issue fines, suspend or revoke businesses’ operating licenses, impose jail sentences, and cause serious reputational harm. In one recent example, Nationwide Building Society was fined £44 million (approx. $59 million) by the UK’s Financial Conduct Authority (FCA) for deficiencies in its AML processes, including weaknesses in its financial crime systems and controls and inadequate transaction monitoring.
To reduce regulatory, legal, and financial risks, companies need to implement risk-based, compliant transaction monitoring throughout the customer lifecycle.
Let’s explore what transaction monitoring is and how companies can stay compliant in 2026. We’ll focus mostly on the regulated institutions.
What is transaction monitoring?
Transaction monitoring involves the ongoing, and where applicable, real-time monitoring of financial transactions and account activity to identify unusual or suspicious behavior that may indicate money laundering or related financial crimes. This includes reviewing data such as deposits, withdrawals, transfers, transaction frequency, transaction size, and counterparties.
The goal of transaction monitoring is to detect patterns, anomalies, or inconsistencies that may signal illegal activity and require further investigation.
Transaction monitoring can help identify financial activity potentially linked to crimes such as:
- Money laundering
- Terrorist financing
- Fraud
- Sanctions evasion
- Proliferation financing
- Other forms of financial crime
When suspicious activity is detected, the system generates alerts that are reviewed by compliance analysts. If the activity is deemed suspicious or if there are reasonable grounds to suspect it relates to a predicate offense, the institution is legally mandated to submit reports to the competent Financial Intelligence Unit (FIU), such as Suspicious Activity Report (SAR) or Suspicious Transaction Report (STR) in accordance with applicable local regulations.
What is AML transaction monitoring?
AML transaction monitoring refers to the use of transaction monitoring systems specifically to detect and investigate potential money laundering and related financial crimes. It is a required control for organizations subject to anti-money laundering (AML) regulations, as well as broader financial crime frameworks such as countering the financing of terrorism (CFT/CTF) and countering proliferation financing (CPF). These requirements apply to banks, payment institutions, Virtual Asset Service Providers (VASPs), and other obliged entities.
Transaction monitoring vs. transaction screening: Key differences
Transaction monitoring and transaction screening are related but serve different purposes in financial crime compliance.
Transaction screening checks transactions and/or counterparties before or during processing to ensure that the parties involved are not listed on sanctions lists, watchlists, or other restricted-party databases. Screening helps prevent prohibited transactions from taking place.
Transaction monitoring, on the other hand, analyzes current and historical transactions as well as patterns of activity over time. Its purpose is to detect suspicious behaviors or transaction patterns that may indicate money laundering or other financial crimes.
In simple terms:
Transaction screening verifies whether a transaction involves sanctioned or restricted parties.
Transaction monitoring analyzes transaction behavior to identify suspicious financial activity across the customer lifecycle.
Why transaction monitoring is required by law
Transaction monitoring is legally required for AML-obliged institutions in many jurisdictions. This includes, but is not limited to:
- Banks (Challenger, Neo, and Traditional banks)
- Money lending services (B2B and B2C)
- Investment firms
- Transfer companies
- FinTech companies
- Crypto exchanges
- Brokerage firms
- InsurTech
- Real estate agents
- Casinos and online betting platforms
- Legal and accounting firms
In the banking industry, AML transaction monitoring is essential for detecting and preventing illicit activities such as money laundering, terrorist financing, and fraud. For this reason, regulators around the world have imposed strict AML due diligence requirements on financial institutions and other high-risk businesses through regulations, such as the US Bank Secrecy Act and comparable AML/CFT frameworks in other countries.
Leading US bank TD Bank provided a notable example of why these laws are needed in October 2024. It agreed to pay over $3 billion in penalties for allowing illegal activities (including the laundering of over $400 million from fentanyl sales) to go undetected due to inadequate transaction monitoring systems.
Effective transaction monitoring can help spot and stop this sort of activity at an early stage, which is why it is one of the most important AML compliance requirements for regulated entities.
How AI-powered AML transaction monitoring prevents fraud, financial crimes, and money laundering
Companies can avoid losses related to fraud, investigations, legal proceedings, and consumer refunds by establishing comprehensive AML transaction monitoring. It ensures that suspicious transactions are quickly identified and, where possible, blocked and reported.
As transaction volumes grow and financial crime schemes become more sophisticated, traditional rule-based monitoring systems often struggle to keep up. AI-powered transaction monitoring helps organizations analyze large volumes of data in real time and identify complex behavioral patterns that may indicate fraud or financial crime.
The monitoring process can also be enhanced through login analysis, password recovery monitoring, and other signals. This provides additional data points to help identify fraud patterns or other suspicious activity. Some solutions combine all these data points using artificial intelligence trained to detect suspicious behavioral patterns and activities.
Failing to implement transaction monitoring systems can have severe consequences. Between June 2016 and December 2020, Metro Bank failed to monitor over 60.5 million transactions totaling more than $65 billion, which ultimately led to a $21.5 million fine.
How AML transaction monitoring protects revenue & reduces compliance costs
Modern transaction monitoring using AI automation can reduce compliance costs and protect revenue in ways such as:
- Automation of monitoring processes: Reduces manual work for compliance teams.
- Fewer false positives: Modern systems improve alert quality and reduce unnecessary investigations.
- Lower operational workload: Compliance teams can focus on higher-risk cases.
- Detection of suspicious activity: Helps identify potential fraud and financial crime.
- Reduced risk of regulatory penalties: Supports compliance with AML reporting requirements.
- More efficient compliance operations: Monitoring systems help organizations scale compliance as transaction volumes grow.
Key regulatory frameworks and bodies
Effective transaction monitoring must align with AML compliance requirements set by regulators, including the processes to be followed and the consequences for non-compliance.
Here are some of the key regulations and internationally recognized guidelines for AML transaction monitoring:
- FATF Recommendations. The Financial Action Task Force (FATF) is an intergovernmental organization that sets widely adopted recommendations for AML and Counter-Terrorist Financing (CTF), including customer due diligence and ongoing monitoring expectations covered in Recommendation 10.
- US. The Bank Secrecy Act (BSA) is a landmark US legislation that requires financial institutions to assist government agencies in detecting and preventing money laundering. Key Bank Secrecy Act AML requirements include filing Currency Transaction Reports (CTRs) for transactions over $10,000 and Suspicious Activity Reports (SARs) for any suspicious transactions. The key US government body is FinCEN, which issues implementing regulations and guidance.
- UK. The key UK AML regulations are the Money Laundering, Terrorist Financing and Transfer of Funds (Information on the Payer) Regulations 2017 and the Proceeds of Crime Act 2002 (POCA). These regulations impose requirements such as taking a risk-based approach to AML and reporting suspicious transactions to the National Crime Agency (NCA).
- EU. Anti-money laundering rules in the EU are contained in the ‘EU AML package’, which includes Regulation 2024/1624 and Regulation 2024/1620. These instruments introduce harmonized rules on customer due diligence, ongoing monitoring, and reporting, and include measures such as capping large cash transactions (for example, at €10,000), subject to local implementation.
- LATAM. Many Latin American countries have AML laws, including transaction monitoring requirements. For example, Brazilian Central Bank Circular 3,798/20 requires financial institutions to implement AML/CTF processes, including transaction monitoring and reporting suspicious transactions to the Financial Activities Control Council (COAF). In Argentina, Law No. 25,246 (as amended, including by Law No. 27,739) requires “Obligated Subjects” to monitor customer transactions and report suspicious operations to the Financial Information Unit (UIF), while in Uruguay, Law No. 19,574 establishes AML duties such as customer due diligence, ongoing monitoring, and suspicious activity reporting.
- APAC. Transaction monitoring requirements vary across the Asia Pacific region. For example, in Singapore, payment providers must implement transaction monitoring for their customers under the Payment Services Act 2019, while in the Philippines, transaction monitoring requirements are set out in the Anti-Money Laundering Act of 2001 (Republic Act No. 9160) and its implementing rules and regulations as amended.
Penalties for AML non-compliance
Organizations are legally obligated to follow AML compliance requirements. Failure to do so can result in substantial fines and legal actions. In March 2025, Robinhood Markets had to pay $29.75 million to settle probes by the Financial Industry Regulatory Authority (FINRA), including failing to respond to potential misconduct indications.
Not being compliant with AML regulations can have severe consequences, including but not limited to:
- Monetary penalties. Financial institutions face substantial AML fines and penalties, such as forfeiting revenue, if they aren’t compliant. In the US, federal banking regulators can impose civil penalties ranging from $5,000 per violation to $1,000,000, or 1% of the financial institution's assets, whichever is greater, for each day the violation continues.
- Criminal charges. Individuals and entities can face criminal charges, leading to imprisonment. Criminal penalties for willful violations of the Bank Secrecy Act (BSA) can include fines up to $250,000 and imprisonment for up to five years.
- License revocation or suspension. Regulatory authorities can also carry out AML enforcement actions. For example, they can refuse, cancel, or suspend the registration of service providers presenting unacceptable risks of money laundering or other serious crimes.
Transaction monitoring process flow
AML transaction monitoring processes must be carefully designed so that all necessary information is collected, the proper analysis is carried out, and the required actions are taken for full regulatory compliance. Key steps in the transaction monitoring process include:
Data collection and customer profiling
Before transaction monitoring can be carried out, businesses need to understand who their customers are. Customer risk assessments analyze information collected during onboarding to assign a particular risk level to the customer. This process is called ‘Know Your Customer’ or ‘Know Your Business’ for business clients. Risk levels can be based on country of origin (low, medium, and high-risk countries, for example) or any other factor relevant to the company—for instance, age, nature, and intended purpose of the business relationship, etc.
Based on these risk assessments, companies then determine the type of Customer Due Diligence (CDD) for AML that should be applied. If risk is determined to be low, Simplified Due Diligence (SDD) can be applied. If higher risk is assessed, Enhanced Due Diligence (EDD) may be required, which means asking for additional information or documents during onboarding or conducting transactions, such as source of funds or wealth, etc.
💡In line with FATF Recommendation 10, this due diligence is not a one‑off exercise and must be supported by ongoing monitoring of transactions to ensure that activity remains consistent with the customer’s risk profile
A customer will be assigned a risk profile following KYC for AML transaction monitoring purposes. This risk profile will determine the level of monitoring a customer is placed under, and factors such as regular transaction data analysis will be used to assess whether a customer’s assigned risk profile remains appropriate.
Rule-based detection and threshold setting
AML rules-based monitoring defines what transactions should be considered suspicious and flagged for investigation. Transaction monitoring rules can incorporate various criteria, including those set by regulators, such as transaction value thresholds.
To confront the spread of such activities, companies should focus on the following general factors when setting AML transaction monitoring rules and conducting ongoing monitoring:
- Unusual transaction amounts
- Unusual series of transactions (e.g., a number of cash credits)
- Unusual geographic destination or origin of a payment
- Known threats or typologies
Batch vs. real-time transaction monitoring
In the context of AML, the choice between batch vs real-time transaction monitoring significantly impacts an organization's ability to detect and prevent fraudulent activities.
According to the Guidance for the UK financial sector, there are two approaches to transaction monitoring:
- Real-time transaction monitoring. Carried out as the transaction takes place, real-time AML monitoring flags anomalies instantly so suspicious transactions can be blocked. This means fraudulent transactions can be proactively prevented, reducing the risk of regulatory breaches.
- Batch transaction monitoring. Carried out after the transaction takes place, which can be useful for identifying patterns and trends of criminal activities. Also known as ‘post-transaction monitoring’, this approach is slower at detecting fraud, produces more false positives, and isn’t able to prevent real-time money laundering schemes. Batch processing can increase the risk of compliance breaches and regulatory action.
Machine learning and AI in transaction monitoring
Monitoring financial transactions at scale is increasingly difficult using manual processes alone. Human analysts can miss suspicious activity when reviewing large volumes of transactions, while traditional rule-based systems often rely on predefined scenarios that may fail to detect new or evolving financial crime patterns.
AI-powered transaction monitoring enhances traditional systems by analyzing large datasets and identifying hidden relationships between transactions, accounts, and behaviors. Unlike basic automation, AI models can detect subtle anomalies, similarities, and patterns that may indicate fraud, money laundering, or other financial crimes.
For example, AI systems can identify unusual behavioral patterns across millions of transactions in real time—something that would be impossible for human analysts to perform manually. By continuously learning from new data, machine learning models can also adapt to evolving criminal tactics and improve detection accuracy over time.
AI can also support compliance teams in several additional ways beyond transaction monitoring itself. For instance, AI tools can analyze transaction patterns to suggest new monitoring rules that may strengthen existing controls. Some systems can even generate rule logic automatically based on natural-language instructions from compliance teams.
In investigation workflows, AI can assist analysts by summarizing suspicious activity cases and generating structured reports that support regulatory filings, such as suspicious activity reports submitted to financial intelligence units (FIUs). AI tools can also help compliance teams stay informed about regulatory changes by reviewing new regulatory publications and suggesting updates to monitoring frameworks.
These capabilities allow organizations to move beyond static rule-based monitoring toward more adaptive, data-driven approaches to financial crime detection.
💡Regulators increasingly accept the use of AI and advanced analytics in AML, provided firms can demonstrate appropriate model governance, explainability, validation, and human oversight
How AI reduces false positives in AML monitoring
AML false positives can be costly for businesses that need to investigate them, as well as frustrating for legitimate customers who may have their transactions blocked or accounts frozen if they are flagged as acting suspiciously.
AI can reduce false positives by using more flexible rule sets to identify suspicious activity and by adjusting monitoring rules to customers' risk profiles. AI can also use more context-based approaches, such as behavioral analytics, to tailor its monitoring to each individual customer.
Limitations of traditional rule-based systems
Rule-based monitoring remains a fundamental component of AML transaction monitoring. Clearly defined rules and thresholds help organizations detect many obvious indicators of financial crime, such as unusually large transactions or activity involving high-risk jurisdictions. In practice, rule-based systems can identify the majority of suspicious cases and are essential for ensuring regulatory compliance.
However, rule-based monitoring can sometimes generate a high number of false positives when rules are too rigid or applied without sufficient context. For example, legitimate transactions may be flagged simply because they exceed predefined thresholds, even when the customer presents a low money-laundering risk. As transaction volumes grow and financial crime tactics become more complex, rules alone may struggle to detect subtle or emerging patterns of suspicious activity.
How machine learning supports traditional systems
Machine learning models complement rule-based monitoring by helping identify more complex or difficult-to-detect risks. While rules focus on predefined indicators, machine learning can analyze large volumes of data to detect anomalies, hidden relationships, and behavioral patterns that may indicate suspicious activity.
By learning from historical transaction data, machine learning models can better understand customer behavior and risk profiles, which can help reduce false positives and improve detection accuracy. For example, ML-based systems can recognize when a transaction that appears unusual according to static rules may actually be consistent with a customer's typical activity.
💡In practice, the most effective AML monitoring systems combine both approaches: rules provide clear controls for detecting obvious risks, while machine learning helps uncover more subtle or evolving financial crime patterns. Together, they create a more balanced and effective transaction monitoring framework.
AI implementation checklist for transaction monitoring
To ensure effective integration of AI into AML transaction monitoring, organizations should consider the following steps:
- Conduct a comprehensive risk assessment
- Develop a clear AI integration strategy
- Ensure high-quality data management and governance
- Select appropriate AI and machine learning technologies
- Implement continuous monitoring and model evaluation
- Provide training and awareness programs for compliance teams
- Establish a robust governance and accountability framework
- Continuously improve models based on new risks and regulatory developments
Alert generation and case management
Case management in AML is the process of investigating, recording, and reporting suspicious activity. When suspicious activity is detected, whether by a human or an automated system, it should trigger an AML alert. Management of this alert will involve reviewing the reason for the alert and any relevant contextual information (e.g., previous alerts connected to the same account or account holder). Depending on the applicable legal framework and the level of suspicion meeting the relevant reporting threshold, an FIU report (a SAR or STR) will need to be generated and submitted with all required information. All information about the alert and the actions taken will need to be documented according to an organization’s risk framework.
Much of the process of AML alert investigation and case management can be automated, including generating human-readable reports for quick review. Using modern AI-driven AML software to assist with this process helps to ensure alerts are actioned promptly, SARs are generated and submitted in a timely manner, and all regulatory requirements are met consistently.
Suspicious Activity Reports (SARs): When and how to file them
❗The biggest challenge companies usually face is not failing to monitor transactions, but failing to report suspicious activity in time. This is because a large part of transaction monitoring regulations focuses on reporting suspicious activities or transactions to financial intelligence units (FIUs).
Firms are obligated to file a FIU report, such as Suspicious Activity Reports (SARs) or Suspicious Transaction Reports (STRs), depending on the jurisdiction, when illegal activity has taken place (or when suspicious activity has met the relevant reporting threshold, which varies from country to country). Therefore, a quick and easy suspicious activity reporting tool is a must-have. This makes it easier to inform regulators about risky activities indicative of money laundering, tax evasion, fraud, and other financial crimes, while ensuring you follow the right process for filing an SAR in every jurisdiction where you operate.
What triggers a Suspicious Activity Report and how to file a SAR for AML will depend on the regulatory requirements in your country. This will typically include triggers such as transactions involving high-risk countries and transactions above a certain threshold set out in local law or regulatory guidance (In the UK, for example, there is no minimum monetary threshold for a SAR under the Proceeds of Crime Act 2002; the obligation is triggered by the 'suspicion' of criminal property regardless of the amount).
Behavioral analytics and customer baseline profiling with AI
Using behavioral analytics in AML can significantly improve transaction monitoring. AI tools can analyze customers’ normal behavior and use this to determine whether specific transactions fit these patterns or are anomalies that could indicate financial crime.
Transaction monitoring typologies
Transaction monitoring typologies are known patterns of financial crime that AML teams and technical solutions use to identify suspicious activity. These patterns are often called ‘money laundering typologies’ or ‘AML typologies’. These typologies are, effectively, money laundering ‘red flags’ that can be used to identify potential instances of money laundering.
Common money laundering red flags in transactions
AML red flags in transactions include:
- Suspicious transaction patterns. Such as large cash deposits or withdrawals, rapid movements of funds in and out of accounts, and frequent transactions just below reporting thresholds.
- Behavioral anomalies. For example, large transactions or multiple transactions in a short space of time that are not consistent with the customer’s established behavior.
- Geographic inconsistencies. Such as a customer sending funds to or receiving them from high-risk jurisdictions with which they have no obvious link.
- High-risk or obscure sources of funds. For example, funds from high-risk jurisdictions or individuals, use of intermediaries and shell companies, and payments from or to parties with no explicable connection to the customer.
These AML typologies can be important money laundering indicators, so systems must be calibrated to detect them, generate alerts, and kick off appropriate follow-up actions.
Crypto-specific AML transaction monitoring typologies
There can be specific challenges involving crypto and AML monitoring, so businesses need to be aware of particular red flags to look out for in crypto transaction monitoring. These can include:
- Use of anonymity-enhancing technology. Such as privacy coins and crypto mixers/tumblers to obscure the source of funds.
- Chain hopping. Where funds are rapidly converted between different cryptocurrencies to create a fractured audit trail.
- Rapid cashing out. Where a customer receives cryptocurrency and then immediately converts it to fiat currency.
Virtual asset AML is a specialist area of expertise, so it is important that crypto businesses and those dealing with virtual assets have the right processes in place to ensure their transaction monitoring is fit for purpose. For example, techniques such as Blockchain AML can be used to track digital assets in real time using transparent, decentralized ledger technology.
AML transaction monitoring system implementation
When considering how to implement AML transaction monitoring, businesses should take the following steps:
Step 1: Conduct an institutional risk assessment
It is essential in AML to apply a risk-based approach. Businesses should carry out a formal AML risk assessment, as well as look at risks for terrorist financing and other financial crimes. The risks vary based on the business’s products, customer profiles, and the nature and frequency of transactions.
Once assessed in an institutional risk assessment, these risks should form the foundation of a transaction monitoring implementation system. For example, once a business identifies which types of customers present a higher risk of money laundering, they can set a more frequent and intensive ongoing monitoring of their transactions. Move away from a heuristic rules-based approach to a risk-based approach, with AI and ML data ingestion and flagging capability.
Step 2: Define customer segmentation and risk scoring
Customer risk assessments analyze information collected during onboarding to assign a particular risk level to the customer. This is known as AML customer segmentation and risk scoring. These risk levels assigned in AML risk scoring can be based on country of origin (low, medium, and high-risk countries, for example) or any other factor relevant to the company—for instance, age, nature, and intended purpose of the business relationship, etc.
Customer risk scoring for AML is essential because it allows resources to be properly allocated to high-risk customers while minimizing any friction for low-risk customers. Based on these risk assessments, companies then determine the type of Customer Due Diligence that should be applied. If risk is determined to be low, Simplified Due Diligence (SDD) can be applied. If higher risk is assessed, Enhanced Due Diligence (EDD) may be required, which means asking for additional information or documents during onboarding or conducting transactions, such as source of funds or wealth, etc. Risk ratings and segmentation should be reviewed periodically, and when trigger events occur (such as material changes in ownership, products used, or transactional behaviour), to ensure that monitoring remains aligned with the customer’s current risk profile.
Suggested read: AML & Fraud Risk Assessment: Risk Matrices, Risk Scoring, and Best Practices
Step 3: Configure monitoring rules and thresholds
Implementing advanced anti-money laundering transaction monitoring strategies requires the development of rules specific to an organization's risk profile. Best practices for transaction monitoring rules creation include:
- Tailoring rules for specific risks. Customize AML transaction monitoring rules to address the unique risks associated with different customer segments. This significantly helps with detection accuracy. This includes AML threshold configuration, making sure the rules comply with threshold reporting requirements for specific jurisdictions.
- Leverage advanced technologies. Incorporate AI and Machine Learning to analyze large datasets, identify complex patterns, and adapt to evolving financial crime tactics because this improves the scalability and precision of monitoring systems. Where such technologies are used, firms should also implement appropriate model governance, testing, and explainability controls in line with regulatory expectations.
- Conduct rigorous testing. Before deployment, thoroughly test new rules using historical data to inspect their effectiveness and minimize false positives.
- Implement continuous monitoring. Establish a process for ongoing evaluation and refinement of monitoring rules to respond to emerging threats and regulatory changes. This way, you can stay ahead of new financial crime methodologies.
Step 4: Integrate AI/machine learning for anomaly detection
AI and machine learning strengthen AML transaction monitoring by finding anomalies in real time and adapting to new fraud patterns. Anomaly detection in AML works by understanding customers’ normal patterns of behavior, then detecting any deviations from those patterns or ‘anomalies’. AI transaction monitoring solutions can make this more effective through rapid analysis of much larger volumes of transaction data, sophisticated behavioral analysis, and quick identification of anomalies.
Businesses should train AML machine learning models on historical transaction data to recognize suspicious behaviors, such as unusual transaction volumes, rapid fund transfers, or deviations from typical customer activity. AI-powered systems continuously learn from new data, reducing false positives and improving risk detection. For instance, clustering algorithms can identify hidden connections between seemingly unrelated transactions, while natural language processing (NLP) can analyze unstructured data for risk signals.
Step 5: Establish alert review and case escalation workflows
Suspicious transaction alerts must be reviewed so that appropriate action can be taken. AML alert management should be part of your case management protocol to ensure this is carried out promptly and in line with regulatory requirements.
Increasingly, case management for AML relies on workflow automation. This means using software operating within defined rules to trigger actions that form part of a workflow. AML workflow automation can reduce manual case handling workloads while also cutting the potential for human error.
Step 6: Automate SAR filing and regulatory reporting
FIU reports (SARs or STRs) must be filed with the relevant authorities if a transaction meets the reporting threshold in a jurisdiction where you operate. Any failings in SAR filings for AML purposes can result in serious consequences, so your processes must ensure that these reports, and any others required by regulations, are submitted promptly and accurately.
AML regulatory reporting requirements can be automated with modern AML systems. This means compliant reports will be automatically generated whenever a transaction meets the reporting threshold, reducing the risk of human error and improving compliance.
Step 7: Conduct ongoing audits and rule refinement
AML continuous monitoring requires organizations to regularly review and improve their monitoring systems and controls. There must be appropriate mechanisms for the oversight, review, and approval of monitoring processes and parameters, including transaction monitoring rules.
There must be appropriate mechanisms for oversight, review, and approval of monitoring processes and parameters, including transaction monitoring rules.
Some of these policies may include:
- Defining responsibilities for the company’s staff members
- Measuring the effectiveness and relevance of monitoring arrangements
- Supporting system changes to address evolving money laundering risks
Internal and external AML audits can identify compliance gaps and areas for improvement, allowing systems to continually improve and minimizing the risk of regulatory breaches.
AML transaction monitoring challenges and how to overcome them
Transaction monitoring comes with several AML compliance challenges, including high false positives, evolving fraud tactics, and regulatory compliance burdens. Each industry faces unique risks that need to be accounted for in AML strategies to successfully navigate AML transaction monitoring challenges:
- Banking, financial services, and fintech. These sectors typically process large volumes of digital and cross-border transactions, which increases exposure to risks such as money laundering, layering, fraudulent account openings, and synthetic identity fraud. Common risk indicators include sudden spikes in international wire transfers, transactions just below reporting thresholds, dormant accounts suddenly becoming active, rapid fund movements between multiple accounts, excessive use of prepaid cards, and repeated failed authentication attempts.
- Crypto. Cryptocurrency and virtual assets suffer high exposure to illicit transactions due to pseudonymity and decentralized platforms. Red flags are usually transactions involving high-risk jurisdictions or unhosted wallets, or newly created wallets with large transfers.
- E-commerce & marketplaces. Marketplace challenges are fraudulent chargebacks, fake merchant accounts, and money laundering through refund schemes. Signs of risk involve mismatched billing/shipping addresses, multiple transactions from the same IP but different payment methods, and unusually high-value purchases from new accounts.
- Insurance management. Money launderers may use insurance policies and investment accounts for layering. Indicators are typically early policy cancellations with large cash withdrawals, frequent beneficiary changes, and lump-sum contributions with no clear source of funds.
- Trading and investment platforms. Online trading platforms may be exposed to market manipulation and money laundering through rapid buying and selling of assets to obscure the origin of funds. Risk indicators include unusually high trading volumes with little economic rationale, frequent deposits and withdrawals without meaningful trading activity, and coordinated trading across multiple linked accounts.
- iGaming and online gambling. The iGaming sector faces risks related to money laundering, fraud, and bonus abuse. Suspicious indicators include frequent deposits followed by minimal gameplay and rapid withdrawals, use of multiple accounts by the same user, unusually large wagers inconsistent with a player’s profile, and repeated use of different payment methods across related accounts. Operators must ensure compliance with both gambling licenses and AML/CTF statutes, which often have overlapping but distinct reporting requirements.
Managing false positives in AML systems
Transaction monitoring false positives occur when legitimate transactions are flagged as suspicious. Reasons for this include overly rigid criteria that cannot be easily varied to match the risk profiles of different customers. Companies then waste resources investigating each flagged transaction to determine whether it is suspicious, and customers’ transactions may be delayed or blocked if they are flagged.
More flexible transaction monitoring systems using AI can significantly reduce AML false positives by allowing monitoring rules to be more flexible. Low-risk customers can, therefore, receive less stringent monitoring, reducing the likelihood of their transactions being wrongly labelled suspicious. However, if a low-risk customer’s behavior changes to indicate a higher risk, their risk profile and monitoring requirements can be adjusted instantly to ensure proper scrutiny.
Regulatory complexity across jurisdictions
Where companies operate across multiple countries, their AML systems need to be able to adapt to the regulatory requirements in each jurisdiction. Transaction monitoring solutions should have the capacity to ensure compliance with different regulatory requirements, so there are no compliance gaps.
❗For example, a transaction threshold that triggers reporting in one country may differ from the threshold required in another jurisdiction, meaning monitoring rules and reporting procedures must be adjusted accordingly.
Choosing an AML transaction monitoring solution
Choosing the best AML transaction monitoring software is a hugely important decision. You need to find a solution that meets all regulatory requirements and integrates with your existing systems and processes, while remaining cost-effective.
Automated transaction monitoring software reviews and analyzes user actions in real time, which saves company resources. Meanwhile, only some suspicious cases are assigned to the compliance team. Sometimes, a combination of both is necessary, especially in firms with a high volume of transactions.
A good example of this is HSBC, which utilizes artificial intelligence in its AML transaction monitoring solution to screen over a billion transactions a month for signs of financial crime, which helps in reducing false positives and manual reviews. It also employs AI to enhance the precision of financial crime detection, reducing alert volumes and the time spent on investigations.
JPMorgan Chase has invested heavily in AI and RPA technologies to improve business performance and operations by focusing on automating compliance and audit processes.
Key features to look for in a transaction monitoring system
When selecting the right AML transaction monitoring solution, it’s important to choose a system that brings all essential controls and checks together in a single workflow.
To help organizations evaluate providers effectively, we’ve compiled a complete set of questions to ask any AML transaction monitoring vendor. This blueprint covers the most important transaction monitoring software features required for a robust, compliant monitoring system, including:
- Transaction monitoring engine
- Rule logic and typology coverage
- Machine learning and behavioral analytics
- Case management and alert handling
- FIU (SAR/STR) reporting
- Regulatory alignment (FATF, AMLD6, FinCEN, MAS, FCA)
- Model governance and explainability
- Data security and certifications
- Integrations and data ingestion
- Commercials and SLAs
Check out the AML Transaction Monitoring Vendor RFP Blueprint.
Build vs. buy: In-house vs. vendor AML solutions
While some larger businesses may choose to build their own, in-house AML transaction monitoring solutions, most companies will buy AML software to meet their needs.
Advantages of working with an established vendor of AML systems include:
- Cost-effectiveness. It will generally be much less expensive to buy a solution than to cover the cost of developing one from scratch.
- Tried-and-tested solutions. A bought-in solution will usually have been used by many other companies, so any problems should have been identified and worked out. You should also be able to see real-world data and testimonies about how the system performs.
- Swift implementation. When you buy a system, it can normally be implemented very rapidly, giving you immediate support. Building an effective AML solution in-house can take years, including the time for development, testing, and bug fixing.
- Easy integration with other systems. Vendor software should include APIs that allow easy integration with your existing systems, and the vendor’s support team should assist with this.
- Experienced expertise. Vendors who specialize in AML software should offer high-level expertise both on the technical side of the system and also on all of the regulatory requirements for jurisdictions around the world.
- Regular support. In-house developers are likely to be pressed for time as they have to work across multiple systems. Software vendors should offer ongoing support as part of their contract, ensuring you get the technical help you need when you need it.
- Frequent updates. AML software must be constantly updated to stay on top of the latest threats and regulatory changes. In-house developers may struggle to keep pace, whereas a vendor-supplied solution should be constantly updated as standard.
Sumsub’s transaction monitoring software allows you to detect all suspicious activities with one solution—from sign-up to their journey, with ongoing real-time monitoring.
Transaction monitoring FAQ
-
What is transaction monitoring in banking?
Transaction monitoring in banking is an ongoing security process that helps companies detect suspicious transactions. Transaction monitoring software spots unusual patterns and reviews dubious transfers and transactions made in digital or fiat currencies.
-
How does the transaction monitoring process work?
Any regulated business is obligated to have transaction monitoring in place. The best solutions ensure that monitoring is integral to the entire verification flow, meaning that user, business, and transaction verification are connected. This way, you can use every single available data point to assess users, risks, and suspicious patterns. Transaction monitoring typically consists of the following steps:
- Transaction data transferring
- Detecting suspicious activity
- Reporting
-
What are the red flags in transaction monitoring?
To confront the spread of illegal activities, companies should focus on the following, which are common red flags in transaction monitoring:
- Unusual transaction amounts
- Unusual series of transactions (e.g., a number of cash credits)
- Unusual geographic destination or origin of a payment
- Known threats or typologies
-
What is synthetic transaction monitoring?
Synthetic transaction monitoring is a method of measuring and testing the performance of a system using simulated data that mimics the behaviors of real users. This can expose potential gaps before using the system in a real-world setting, allowing any issues to be resolved proactively.
Relevant articles
- Article
- 2 weeks ago
- 12 min read
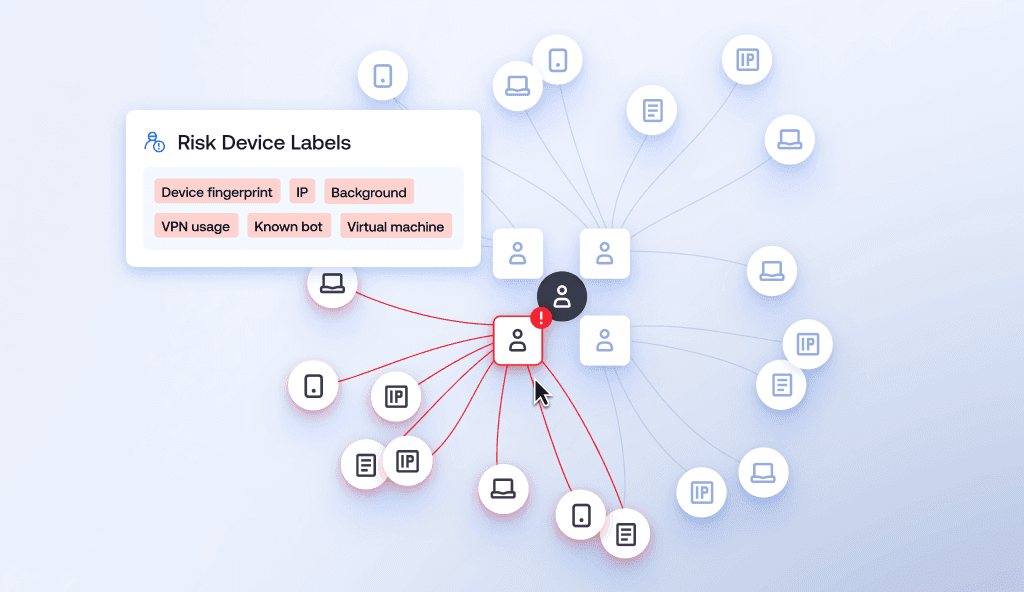
Learn how device intelligence assesses device risk in real time using technical signals and device fingerprinting—without disrupting the customer exp…
- Article
- Mar 27, 2026
- 8 min read
Hospitality fraud trends are evolving. Learn the threats within the hospitality sector today and what can help stop scams, chargeback abuse, and loya…
What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.



