- May 21, 2025
- 9 min read
Liveness Detection: A Complete Guide for Fraud Prevention and Compliance in 2025
Read all about liveness technology and why it’s your best chance against fraudsters.
According to estimates from Juniper Research, global losses from online fraud will exceed $362 billion between 2023 and 2028. This highlights a critical need for advanced, strong identity verification methods.
At the same time, Know Your Customer (KYC) and Anti-Money Laundering (AML) regulations demand a high level of confidence in the security measures businesses use. Which is why today, biometric liveness detection is part of almost every identity verification solution on the market. Indeed, the global face biometric liveness detection market is projected to surpass $250 million by 2027, according to a 2025 market report from Biometric Update and Goode Intelligence. This reflects rapid growth as businesses—especially in heavily regulated sectors—adopt liveness detection to combat spoof attacks on biometric systems.
Yet, in 2025, the fight between fraudsters and anti-fraud teams is a constant cat-and-mouse game. With the democratization of AI and the rise of fraud-as-a-service, fraudsters are continuously developing new methods to trick biometric verification. When liveness solutions fail, companies can suffer immense reputational and financial losses, not to mention regulatory fines.
In this article, we’re going to dive deep into liveness detection. We’ll cover the types of solutions out there, what makes for a good one, and how fraudsters try to spoof them.
What is liveness detection?
Liveness detection is a security technology used to verify whether a face presented to a camera belongs to a live person who’s physically present at the time of capture. It detects if the facial data submitted during identity verification comes from a real human being—not from a photo, deepfake picture, or video. Liveness is an essential part of many identity verification products due to its usefulness in ensuring that the user is authentic every step of the way.
While not all liveness detection solutions are AI-powered today—many still rely on rule-based methods like detecting blinks, head movements, or light reflections—AI-enhanced systems are quickly becoming the industry standard. AI-powered liveness detection can analyze subtle signs of life, such as micro-movements, skin texture, reflections, and depth cues. AI-powered liveness is far more effective at detecting advanced spoofing attempts like deepfakes, masks, or video replays. Plus, it continues to improve over time through training on large datasets.
AI-driven fraud and deepfake usage surged fourfold from 2023 to 2024, driven by rapid AI advancements, and it’s a threat that continues to grow and evolve. What’s more, deepfakes accounted for 7% of all fraud in 2024. And advanced AI-powered liveness detection can shield businesses against deepfakes, lookalikes, and doppelgangers, physical and digital images, high-resolution videos, AI-avatars, and more.
Liveness can be implemented in two main forms: active (requiring some kind of user interaction) and passive (analyzing facial data in the background without user input).
Suggested read: What Are Deepfakes, and How Can You Spot Them? (2025)
Active vs. passive liveness detection
Active liveness detection requires user interaction (like blinking or turning the head), while passive liveness detection works in the background without user input, analyzing facial data and behavior to confirm a live presence.
Both methods aim to determine whether a biometric sample comes from a live person, but they differ in approach, user interaction, and implementation complexity. The table below showcases the key differences between the two types of liveness detection.
| Feature | Active liveness detection | Passive liveness detection |
| User interaction | Required (blinking, head turns, or other movements) | None required |
| Detection method | Motion analysis or response to prompts | AI-based image analysis (texture, depth, etc.) |
| User experience | More intrusive; may cause friction | Seamless and frictionless |
| Spoofing resistance | High, depending on implementation | Very high, especially against deepfakes |
| Processing speed | Slightly slower due to user prompts | Generally faster |
| Best use cases | High-risk or high-security environments | Scalable onboarding, mobile-first UX |
How liveness detection works
Modern liveness detection analyzes a person's biometric data using machine-learning algorithms. Most often, it’s associated with facial biometrics.
It works by utilizing a neural network, which is capable of distinguishing between real and ‘fake’ faces. The system scans the applicant’s face, creates a 3D Face Map, and then applies deep-learning to discover intricate structures in the data.
For the user, the process typically entails staring into a camera, performing certain movements or completing specific tasks (such as pronouncing random words), depending on what’s required by a given solution.
Some of the detection techniques include:
- Face motion. Detects natural movements, such as blinking or head turns, to ensure the person is alive.
- Texture analysis. Analyzes skin texture, lighting, and shadows to confirm the authenticity of the face.
- Emotion detection. Captures micro-movements of facial muscles to detect genuine emotions, preventing spoofing attempts like static faces or photos.
- Random tasks. In some cases, users are prompted to perform random tasks, like pronouncing words, to further confirm their presence—this step in particular can significantly strengthen fraud prevention, due to its complexity.
Don’t trust what you see: The deepfake threat is real
The era of simple spoofing attacks using printed photos or masks is over. Today, fraudsters are using advanced AI technologies to create hyper-realistic deepfakes that can deceive even the most vigilant individuals. These synthetic identities are not just a novelty—they're a tool for intricate scams that can lead to significant financial and reputational damage.
According to the Sumsub Identity Fraud Report, the use of deepfakes surged globally in 2023 and, by 2024, had become deeply entrenched—and increasingly accessible—tools for fraud. The number of deepfakes detected worldwide quadrupled between 2023 and 2024, accounting for 7% of all fraud attempts. This trend is expected to continue through 2025 and beyond.
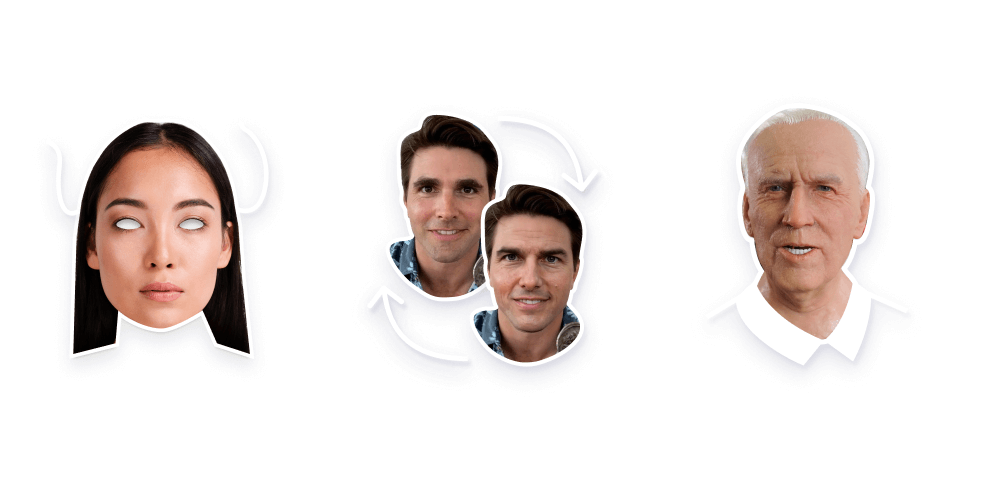
Just this year, Indonesians were swindled by scams using deepfakes of President Prabowo, highlighting how political figures can be impersonated to lend credibility to fraudulent schemes.
And in 2024, a finance worker in Hong Kong was tricked into transferring $25 million after receiving a video call from what appeared to be their company's CFO. The call was a deepfake, meticulously crafted to mimic the executive's likeness and voice.
These are just a few examples that highlight a new, important reality: seeing isn’t always believing anymore. With the rise of deepfake technology, it’s become alarmingly easy to impersonate anyone and to manufacture audio or visual evidence.
Suggested read: From Panic To Expertise
Even the dating world isn’t safe from the pattern—romance scammers have been as active as ever in recent years. In Hong Kong, for example, police have arrested 31 individuals who allegedly used deepfakes to scam people on online dating platforms, leading to HK$34 million in losses.
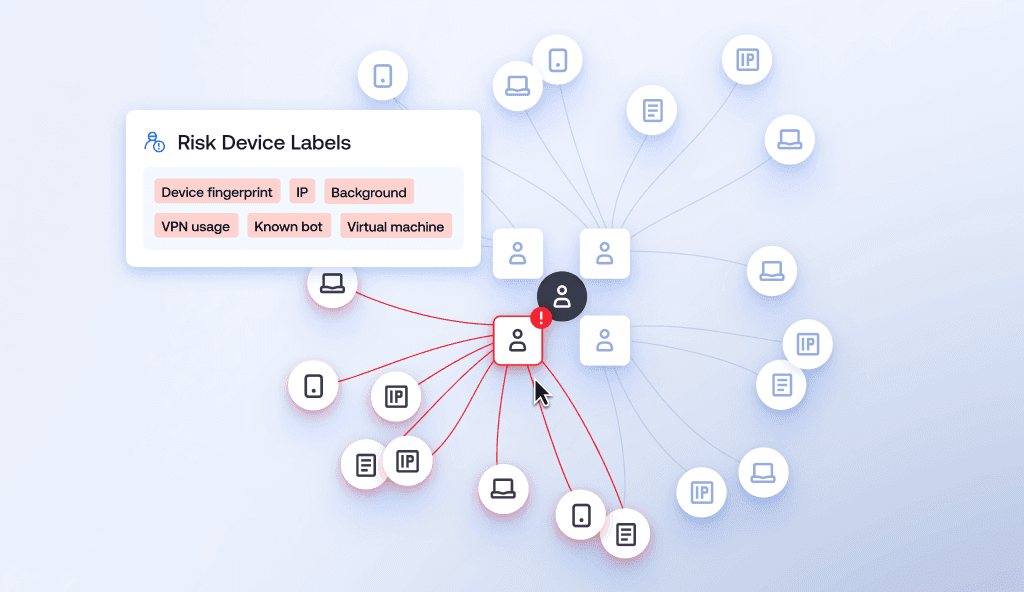
To tackle the growing issue, businesses from both regulated and unregulated industries are recommended to put advanced liveness detection systems in place. These systems are designed to tell the difference between real human interactions and those generated by AI. Advanced liveness systems conduct pixel analysis and pattern recognition technology, which identifies fakes with precision in real-time and analyzes micro-signals to ensure nothing slips through.
By applying strong liveness detection measures, organizations can better protect themselves and their users from falling prey to sophisticated deepfake scams. With digital deception on the rise, verifying the authenticity of user interactions has become not just important—it’s absolutely essential.
Suggested read: Fraud Trends for 2025: From AI-Driven Scams to Identity Theft and Fraud Democratization
Use cases of liveness detection
Liveness detection plays a key role in improving security and preventing fraud across multiple sectors. Some industries where this technology is making a significant impact include:
Fintech and digital banking
In the financial sector, liveness detection is used for remote onboarding and authentication processes. It helps prevent identity fraud by confirming that the person initiating a transaction or opening an account is physically present. This technology is often incorporated into KYC procedures to comply with regulatory requirements and make security stronger. For instance, thanks to Sumsub’s in-house liveness technology, The Kingdom Bank managed to reduce the rate of scam applications in emerging markets.
Healthcare
Online healthcare services utilize liveness detection to verify patient identities during virtual consultations. This way, medical advice and prescriptions are provided to the correct individual, maintaining patient confidentiality and preventing insurance fraud.
Government services
Governments employ liveness detection for various applications, including issuing digital IDs, verifying identities for tax returns, and controlling access to restricted platforms. For example, the US General Services Administration's Login.gov platform faced challenges due to the absence of liveness detection, showing how important it is to meet federal security guidelines and reduce fraud risks.
Education and remote learning
Schools and universities are using liveness detection to verify student identity during online exams and classes. This process helps keep things fair by making sure that the person taking the test is actually the registered student, which reduces the chances of cheating or impersonation.
Dating platforms
Online dating platforms greatly benefit from using liveness detection to prevent deepfake romance scams, which are on the rise. Liveness detection can nip this type of scam in the bud by letting only real people make profiles and making it much harder for scammers to impersonate someone convincingly during identity verification or video calls.
Why is liveness detection important?
Liveness is a core component of most verification solutions—including Non-Doc, Doc-based IDV, and Reusable KYC. It's not just an add-on; it's essential for establishing trust, improving security, and verifying user authenticity at every stage. Liveness helps prevent identity fraud during remote onboarding and authentication, not to mention it also supports regulatory compliance.
Benefits of liveness detection for fraud prevention and compliance
Liveness is an essential part of enhanced security measures, and it supports AML/KYC compliance across various industries.
- Anti-spoofing protection. It helps prevent presentation attacks, such as using photos, videos, or masks to impersonate someone else. According to the National Institute of Standards and Technology (NIST), liveness is a method developed to counter the presentation of fake biometrics at a sensor.
- Stronger security. Liveness detection is considered stronger than many traditional verification methods. By verifying the presence of a live user, liveness detection adds another layer of security to biometric authentication systems and reduces the risk of unauthorized access.
- Regulatory compliance. Implementing liveness detection aligns with compliance requirements for identity verification processes. NIST's Special Publication 800-63B requires credential service providers to employ liveness detection capabilities to ensure that the applicant's facial image used for comparison is "live" and not a spoofing or presentation attack.
- Mitigating identity fraud. Liveness detection checks that a biometric input comes from a real person, which helps prevent spoofing attempts using things like photos, videos, or deepfakes.
- Enhancing regulatory compliance. Implementing liveness aligns with international standards such as ISO/IEC 30107, which focuses on biometric security and presentation attack detection, helping organizations meet global compliance requirements.
- Reducing financial losses. Integrating this technology in identity verification processes has been shown to decrease fraud-related financial losses by stopping fraudulent account access and transactions.
- Building customer trust. Liveness detection helps build trust with users by making sure that the authentication process is secure and reliable. It gives them peace of mind, knowing that their personal information is safe from fraud.
Challenges in liveness detection
Liveness detection is a great way to boost digital security, but putting it into practice isn't without its challenges. These hurdles can impact user experience, system efficiency, and the overall trustworthiness of the verification process.
- False rejections. Legitimate users may be incorrectly flagged as fraudulent due to lighting conditions, camera quality, or unique facial features, leading to potential drop-offs.
- Integration complexity. Incorporating liveness detection into existing identity verification or onboarding systems can be technically demanding and require compatibility with diverse devices and platforms.
- Device and environment variability. Variations in camera quality, network conditions, and user environments can affect the accuracy and reliability of liveness checks.
- Privacy concerns. Collecting biometric data has some regulatory and ethical concerns, especially regarding storage, consent, and protection of sensitive information.
- Spoofing arms race. As spoofing techniques evolve (such as deepfakes and 3D masks), these systems must continuously adapt to stay ahead of increasingly sophisticated fraud attempts.
Future trends in liveness detection
As fraud tactics become more advanced and digital experiences more seamless, liveness detection is also evolving. Here are key trends shaping its future:
Multi-modal liveness detection
Multi-modal systems go a step further from just facial recognition, adding additional biometric indicators such as voice, fingerprint, iris, or behavioral traits (e.g., typing patterns or movement). By layering multiple modalities, these systems significantly reduce the risk of spoofing, improve accessibility, and improve verification accuracy across populations and device types.
Continuous liveness monitoring
Instead of verifying liveness just once during login or onboarding, continuous monitoring confirms that the user is present throughout the session. Continuous checks run in the background, using subtle cues to confirm ongoing presence without disrupting the user. This is especially relevant for sensitive use cases like online exams, telemedicine, or high-value financial transactions, where session hijacking or substitution is a risk.
Cross-sector integration
As liveness technology matures, we can expect broader adoption across sectors—such as a verified digital ID used seamlessly for different industries. A verified user profile authenticated with liveness detection in one sector (such as banking) could be reused securely in another (for example, government e-services or digital healthcare).
AI-driven passive liveness
The shift toward passive liveness detection continues, with more advanced machine learning models capable of making real-time judgments without requiring user action—resulting in a smoother user experience.
On-device processing for privacy
To address privacy concerns and reduce latency, some providers are moving toward processing liveness checks directly on user devices, without transmitting biometric data to external servers.
Hybrid detection models
Combining active and passive methods in a single workflow is emerging as a way to improve accuracy while adapting to different risk levels and use cases.
Liveness detection solutions
In 2024, forged or altered documents—such as fake IDs, passports, and proof of address—were the leading form of identity fraud, accounting for 50% of all fraud attempts, according to the Sumsub 2024 Identity Fraud Report. As fraudsters employ increasingly sophisticated techniques, organizations require robust liveness detection solutions to ensure secure and seamless user verification. Now, more than ever, it’s becoming unavoidable to safeguard against identity fraud.
Sumsub's Liveness solution has successfully passed the iBeta Quality Assurance testing in line with the ISO/IEC 30107-3 standard. The evaluation confirmed the solution's compliance with Level 2 of the Biometric Presentation Attack Detection (PAD) Standard. Notably, it made zero mistakes during testing, validating Sumsub's technology as capable of resisting sophisticated spoofing attempts.
Sumsub has also been named a leader in the First Gartner Magic Quadrant for identity verification. Many platforms have been tricked by AI-enhanced photos, deepfake videos, or pre-recorded videos. We’re here to offer stronger identity protection measures. Here’s how our liveness works:
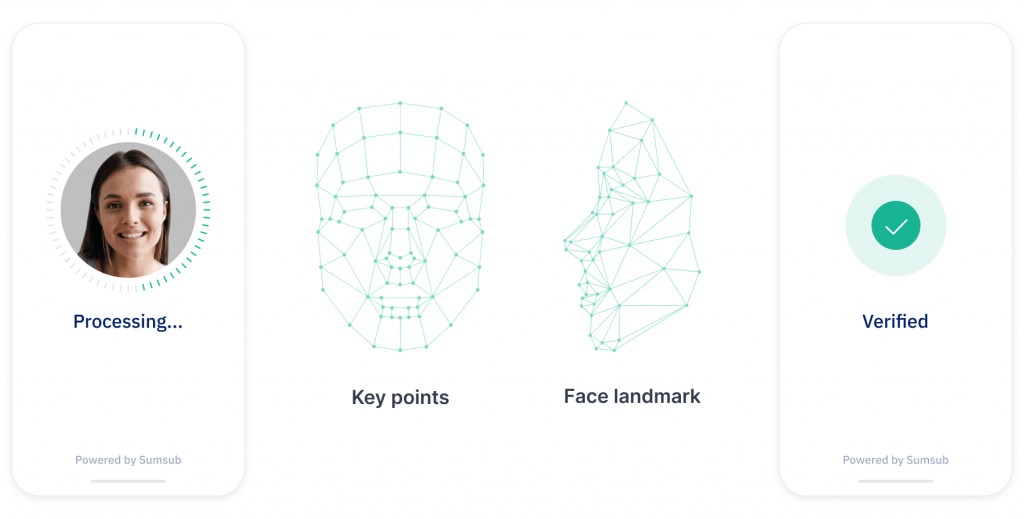
Sumsub offers both active and passive facial biometric liveness, with advanced and secure technology built into both. This allows it to be used for many purposes, including KYC checks, payment fraud prevention, two-factor authentication (2FA), and more. It’s a part of many of Sumsub’s products, such as Non-Doc, Doc-Based IDV, Reusable KYC, and more. Some of its notable features are:
- Deepfake detection. Advanced algorithms identify and prevent AI-generated spoofing attempts, including photo and video deepfakes.
- Device compatibility. Seamless integration across various devices and platforms ensures broad accessibility. It also works well even with slow internet connections.
- Real-time verification. Rapid processing enables swift user onboarding without compromising security.
- Appearance compatibility: The software works seamlessly with beards, makeup, and all ethnicities, helping you achieve pass rates of up to 99%.
We decided not to assign random tasks, as doing so would lower conversion rates. Instead, we employ state-of-the-art technology to detect if fraudsters have hacked a device or inserted a pre-recorded video. This allows us to keep onboarding flows simple while providing bulletproof security.
-
What is liveness detection in biometrics?
Liveness detection is an AI-powered biometric security feature that verifies whether a captured face or fingerprint is from a real person rather than a spoofing attempt like a photo or mask.
-
What is the difference between active and passive liveness detection?
Active liveness requires user interaction, like turning the head, while passive liveness works in the background without requiring any specific action.
-
Why is liveness detection important in face recognition?
It’s important because it helps prevent spoofing attacks and makes sure that facial recognition systems interact with real users, not fake images or deepfakes.
-
How does passive liveness detection work?
Passive liveness analyzes subtle facial cues like skin texture, lighting, and reflections to detect signs of life without user input.
-
Can liveness detection prevent deepfake attacks?
Yes, liveness detection can help prevent deepfake attacks by using advanced AI algorithms to verify that the biometric data comes from a real, live person rather than a manipulated image or video.
Relevant articles
- Article
- 2 weeks ago
- 16 min read
KYC verification explained: learn how Know Your Customer compliance works, including key steps, verification types, global regulations, and best prac…

- Article
- May 13, 2026
- 12 min read
Learn how device intelligence assesses device risk in real time using technical signals and device fingerprinting—without disrupting the customer exp…
What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.