- Feb 18, 2020
- 3 min read
A Guide and Checklist to PCI DSS Compliance
Handling payments requires close attention to the sensitive personal data incorporated into these transactions. Businesses have to hold down the fort not only to ensure customer data safety against cyber-attacks and theft but to prove their alliance with payment and data processing standards, that include PCI DSS and GDPR.
So, here is what an average business has to know in order to stay compliant with payment card industry data security standards and common requirements.
What is a PCI compliance and who is affected
The payment card industry data security standard (PCI DSS) and payment card industry (PCI) compliance are certain operational and technical standards of personal data protection in relation to credit card data processing.
Any business that stores, transmits and processes customer credit card data electronically is bound to incorporate the fitting practices to comply with PCI compliance standards, providing data security for their customers.
Who enforces the PCI requirements
The organization behind, the one that develops and overlooks PCI DSS, is the PCI Security Standards Council (SSC)—an industry standards body. PCI DSS is currently publicly endorsed by five payment card industry giants: Visa, MasterCard, Discover, American Express and JCB International.
Despite implementing PCI DSS is a must for those that handle credit card data, it doesn't have to be formally validated if a payment card processor in question doesn’t strictly demand it.
More to it, PCI DSS helps businesses to stay compliant with regulations that have similar requirements towards data security and privacy—General Data Protection Regulation (GDPR) and the US Gramm-Leach-Bliley Act (GLBA).
How to be compliant with PCI DSS: the checklist
To avoid sensitive financial data from being hacked by fraudsters and stay compliant, businesses need to integrate PCI data security standards—a set of rules split into 6 categories.
- Create a protected network
Abandon the use of default system passwords and security parameters. Store data securely and encrypt cardholder data in case of transmissions across open networks. Implement and maintain a firewall. - Safeguard cardholder data
Introduce robust security controls around all stored user data, use encryption for transmissions across public or open networks. - Consistently manage malware
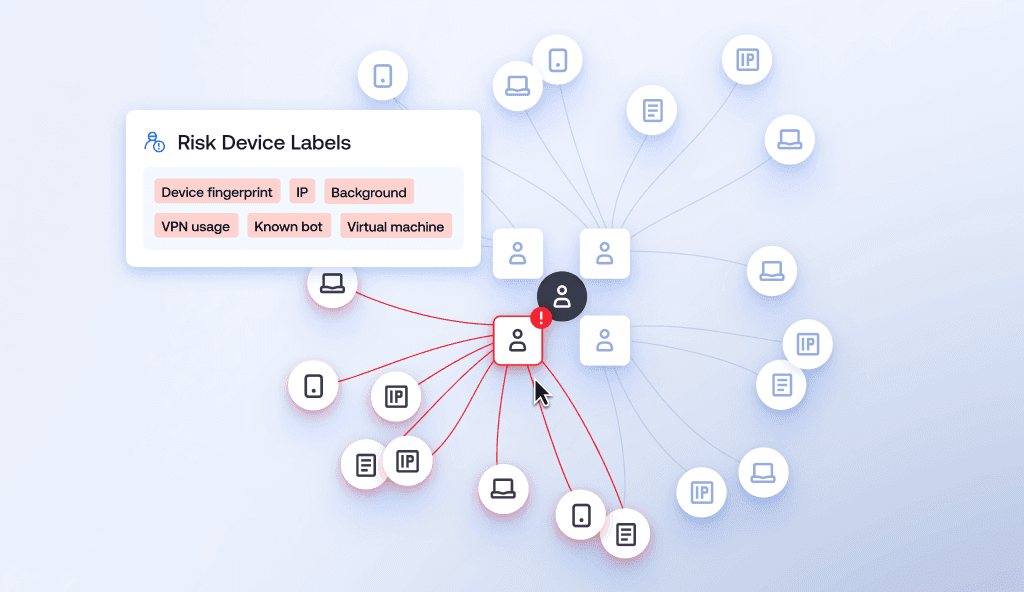
Regularly update antivirus software to keep the system safe from threats, misconfigurations and security breaches. Detect and patch any security vulnerabilities. - Restrict and control the access
Build an authentication procedure around system components. Limit the personnel who can view cardholder data to only the authorised ones and track access. - Constant monitoring
Track and analyze the history of access to the system and scan for suspicious patterns of behaviour. Test your security, map data and perform regular audits to detect flaws. - Maintain a compliant security policy
Create a clear security policy in regards to PCI DSS, internal procedures and responsibilities of the employees. Stay up to date with regulatory norms of the legislation the company is registered with.
To have a truly safe data protection environment the policies have to be maintained secure across the whole transaction life cycle—companies, banks and credit card processors.
The requirements for PCI DSS compliance validation
PCI DSS guidelines separate businesses into 4 levels, based on the transaction volume and data transmission method and set the annual requirements to PCI DSS validation accordingly.
- Level 1: over 6 mln transactions annually across all channels
Requirements: Report on Compliance (ROC) by Qualified Security Assessor (QSA) or Internal Auditor, Attestation of Compliance (AOC) Form.
- Level 2: 1 to 6 mln transactions annually across all channels.
Requirements: Self-Assessment Questionnaire (SAQ), Attestation of Compliance (AOC) Form.
- Level 3: 20,000 to 1 mln e-commerce transactions annually.
Requirements: Self-Assessment Questionnaire (SAQ), Attestation of Compliance (AOC) Form.
- Level 4: less than 20,000 e-commerce transactions annually, all other merchants who process up to 1 mln transactions annually.
Requirements: Self-Assessment Questionnaire (SAQ), Attestation of Compliance (AOC) Form.
Businesses of all levels will also have to initiate a quarterly network scan by an Approved Scan Vendor (ASV).
To give an idea on the penalties that await non-compliant financial businesses, there are many variations – from fines as increased transaction fees to termination of the business entirely.
Aside from the fines that might easily crush small or mid-sized businesses, not complying to PCI DSS subjects firms to actions by state, federal governments and law suits, that cost non-compliant entities a fortune.
To keep up with multiple PCI DSS compliance requirements, companies maintain in-house expertise—integrate various management platforms, that automatically form reports and gather analytical data to submit it to the relevant regulator.
If you like how we think – check out other posts and solutions at Sumsub.
Relevant articles
- Article
- 5 days ago
- 16 min read
KYC verification explained: learn how Know Your Customer compliance works, including key steps, verification types, global regulations, and best prac…

- Article
- 3 days ago
- 10 min read
Money laundering in casinos: the top 6 schemes, key red flags, and AML controls that keep gambling operators compliant.

What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.