- Dec 22, 2025
- 14 min read
Crypto Fraud and AML/CTF Compliance Guide 2026
Everything you need to know about fighting fraud in crypto and staying compliant with AML.
Governments and institutions are intensifying their focus on Anti-Money Laundering (AML) and Counter-Terrorism Financing (CTF) compliance in crypto. There are a number of reasons for this, including:
- The anonymity and decentralized nature of crypto transactions, making them attractive to criminals and
- The substantial losses they’ve incurred for users and businesses in recent years.
According to an FBI report, losses to cryptocurrency fraud in the US alone totaled $9.3 billion in 2024—an 66% increase compared to 2023. Money laundering is another serious concern, and crypto companies remain one of the most common targets for laundering illicit funds. Yet these companies carry full AML compliance responsibility.
Penalties for non-compliance and insufficient transaction monitoring are another pain point for businesses. In 2024, crypto companies faced over $5.1 billion in fines over inadequate AML programs. To mitigate this growing risk, crypto businesses should build robust AML policies and implement necessary compliance measures.
Let’s dive into the specifics of crypto AML compliance and how to get it done right.
What is AML in crypto?
Anti-money laundering (AML) refers to the set of regulations, policies, and procedures designed to prevent and detect money laundering and other illicit activities. Crypto AML measures aim to ensure that cryptocurrency exchanges, wallet providers, and other virtual asset service providers (VASPs) comply with regulatory requirements.
VASPs must therefore comply with applicable AML regulations and licensing requirements in the jurisdictions where they operate. This may include:
- Registering with regulatory authorities
- Obtaining licenses or approvals
- Appointing a Money Laundering Reporting Officer (MRLO)
- Creating effective AML policies and internal controls to manage AML risk
- Taking a risk-based approach to onboarding and monitoring customers
- Carrying out Know Your Customer (KYC) and Know Your Business (KYB) checks for customers to confirm their identities and assess their level of risk
- Ongoing transaction monitoring to identify signs of financial crime
- Recordkeeping
- Reporting suspicious activity to the relevant authorities
- Undergoing periodic audits or examinations to ensure compliance
Suggested read: AML Cryptocurrency Regulations Around the World
Why AML compliance matters in crypto
AML compliance is critical for crypto businesses, not just because it is a regulatory requirement, but also because of the significant financial and reputational harm compliance failures can bring.
The key ways AML compliance breaches can harm crypto companies include:
- Regulatory penalties. These can be huge, for example, CB Payments Limited was fined £3.5 million (~$4.7 million) in 2024 by the UK’s Financial Conduct Authority (FCA). In fact, the average fine for AML compliance breaches in crypto companies stood at $3.8 million in 2025.
- Operational losses. Billions of dollars are lost to crypto fraud each year. This directly impacts crypto companies’ bottom lines due to factors including customer refunds and lost transaction revenue. If a company has come under regulatory scrutiny, its risk and compliance costs may also need to rise as part of its remediation strategy.
- Reputational damage. When AML compliance breaches are uncovered, they become public knowledge. This can lead to a loss of confidence in a business, resulting in tangible harm such as reduced investments and loss of customers.
To properly manage these risks, crypto companies must have effective AML and anti-fraud processes in place.
What is a crypto AML policy?
Anti-Money Laundering (AML) policy outlines the procedures and requirements crypto businesses must follow to verify the identities of their customers and prevent illicit activities such as money laundering and terrorism financing. While specific policies may vary depending on the jurisdiction and the nature of the cryptocurrency business, here is a general overview:
- Customer identification. Cryptocurrency businesses are required to collect personal information from their customers, including government-issued identification documents (e.g., passport, driver’s license) and proof of address (e.g., utility bills, bank statements).
- Identity verification. Cryptocurrency businesses must verify the authenticity of the information provided by customers through various verification methods, such as identity document scans, biometric verification, or third-party identity verification services.
- Risk assessment. Cryptocurrency businesses must conduct risk assessments to determine the level of risk associated with each customer and transaction. This may involve assessing factors such as the customer’s location, transaction volume, and source of funds.
- Enhanced Due Diligence (EDD). For high-risk customers, cryptocurrency businesses are required to conduct enhanced due diligence, which may include additional verification steps, ongoing monitoring, and increased scrutiny of transactions.
- Crypto transaction monitoring and ongoing monitoring. Cryptocurrency businesses must monitor transactions on their platforms for suspicious activity, such as large or unusual transactions, transactions involving high-risk jurisdictions, or patterns indicative of money laundering or other illicit activities.
How AML works in crypto transactions
There are various steps crypto businesses need to go through as part of an effective AML framework. These include:
- Risk assessment. Conducting a risk assessment is essential to identify and mitigate potential AML risks specific to the cryptocurrency business. Implementing risk-based AML measures allows companies to allocate resources effectively and address high-risk areas.
- Customer Due Diligence (CDD). It involves verifying the identities of customers and collecting relevant information to establish their legitimacy. This typically includes collecting personal information such as government-issued ID, proof of address, and, in some cases, conducting enhanced due diligence for high-risk customers. CDD involves assessing the risk associated with each customer and implementing appropriate measures to mitigate those risks. This may include ongoing monitoring of customer accounts and transactions, as well as periodic reviews of customer information.
- Cryptocurrency transaction monitoring. VASPs are required to monitor transactions on their platforms for suspicious activity, such as large or unusual transactions, transactions involving high-risk jurisdictions, or patterns indicative of money laundering or other illicit activities.
- Blockchain analytics. These are used to monitor and assess blockchain transaction data as part of ongoing transaction monitoring. Blockchain analytics can help to spot suspicious activity that may suggest financial crimes, such as money laundering and fraud, could be taking place.
- Travel Rule compliance. In jurisdictions where the Travel Rule applies, VASPs are required to gather, verify, and share certain customer information when carrying out virtual asset transfers on behalf of their clients.
- Reporting suspicious activity. VASPs are obligated to report any suspicious transactions or activities to the relevant authorities, such as financial intelligence units (FIUs), to aid in the investigation and prevention of money laundering and other financial crimes.
Suggested read: Complete Guide to Suspicious Activity Reports
- Compliance programs. VASPs are required to establish and maintain comprehensive AML compliance programs that outline their policies, procedures, and controls for preventing money laundering and complying with regulatory requirements.
Suggested read: AML Compliance Program: The Essential Guide for 2025
- Record-keeping. Cryptocurrency businesses are required to maintain accurate records of customer information, transactions, and AML compliance activities. These records may be subject to inspection by regulatory authorities.
- Employee training. Cryptocurrency businesses must provide AML training to their employees to ensure they understand their obligations and are equipped to identify and report suspicious activity effectively.
Common AML challenges for crypto companies
Common AML challenges for crypto companies include:
- Pseudonymity. This is where customers use false or alternative identities (pseudonyms). The use of pseudonyms can make it harder for crypto companies to correctly identify new and existing customers, and/or to associate them with risk factors tied to their true identity or other pseudonyms. This can compromise an institution’s ability to properly risk assess customers using pseudonyms and assign them an accurate risk rating.
- Decentralized Finance (DeFi). Public blockchains such as Ethereum allow peer-to-peer transactions without a traditional intermediary (e.g., a bank). This can impact crypto firms’ ability to track the source of a customer’s funds. However, this kind of information is publicly available on the blockchain, so it can be traced with the right expertise.
- Tools and tactics that can obscure the origin and destination of funds. Tools such as crypto mixers can be used to blend together cryptocurrencies from many different users, making it harder to trace the source and ownership of the funds. Another common tactic used by money launderers is to break payments up into multiple smaller transactions. This can help to reduce scrutiny by keeping the transaction amounts below the thresholds that automatically trigger further examination under regulatory requirements. It can also allow funds to be quickly moved through multiple accounts to create a confusing audit trail in a process known as “layering”.
These challenges must be considered as part of a business’s AML framework. In particular, they will need to be factored in when taking a risk-based approach to new and existing customers.
Customers should be assessed against these and other risk factors to determine their risk rating. Higher risk customers can then be put through more extensive checks (Enhanced Due Diligence) to weed out those who may be involved in financial crime.
What are the red flags of crypto fraud and money laundering?
Crypto fraud and crypto money laundering (ML) often overlap in behavioral and transactional indicators, since both involve illicit movement of digital assets and attempts to disguise their origin or purpose. However, their underlying intent may differ. Crypto fraud focuses on illegally obtaining assets (e.g., scams, phishing, rug pulls, investment fraud), while crypto money laundering focuses on concealing or legitimizing illicit proceeds (from fraud, ransomware, darknet markets, etc.). Let’s check out the red flags indicative of crypto fraud and of money laundering, which often go hand in hand.
Red flags indicative of crypto fraud
- Crypto fraud typically involves suspicious acquisition or transfer of assets that suggest deception, theft, or scam activity.
- Unusually large or sudden transactions inconsistent with a customer’s known financial profile or trading history.
- Multiple rapid transactions or fund movements through several wallets shortly after deposits, especially to obfuscate the source.
- Transactions involving round numbers, repetitive transfers, or patterns lacking clear economic purpose.
- Sudden influxes of funds from numerous unrelated wallets (potential scam victims).
- Immediate transfers to mixers, tumblers, or privacy coins following suspicious inflows.
- Customer interactions with unregistered or unlicensed exchanges, “investment platforms,” or wallet services.
Check out this article for the full list of crypto scams businesses and users need to be aware of in 2026 and beyond.
Red flags indicative of crypto ML
- Money laundering through crypto involves concealing, layering, and integrating funds derived from criminal activity to make them appear legitimate.
- Unusual or inconsistent transaction volumes given the customer’s known profile or business operations.
- Structured transactions: breaking large sums into smaller amounts to avoid detection thresholds.
- Rapid movement of funds across multiple wallets, exchanges, or chains (chain-hopping) with no economic rationale.
- Use of privacy coins (e.g., Monero, Zcash, Dash) or mixers/tumblers to obscure transaction trails.
- Involvement of geographic hotspots known for weak AML enforcement or high crypto crime rates.
- Cross-border transactions to or from exchanges lacking proper licensing or supervision.
- Use of business accounts or shell companies for crypto transactions inconsistent with declared business activity.
- Politically Exposed Persons (PEPs) or associates transacting in ways unrelated to their official role or declared income.
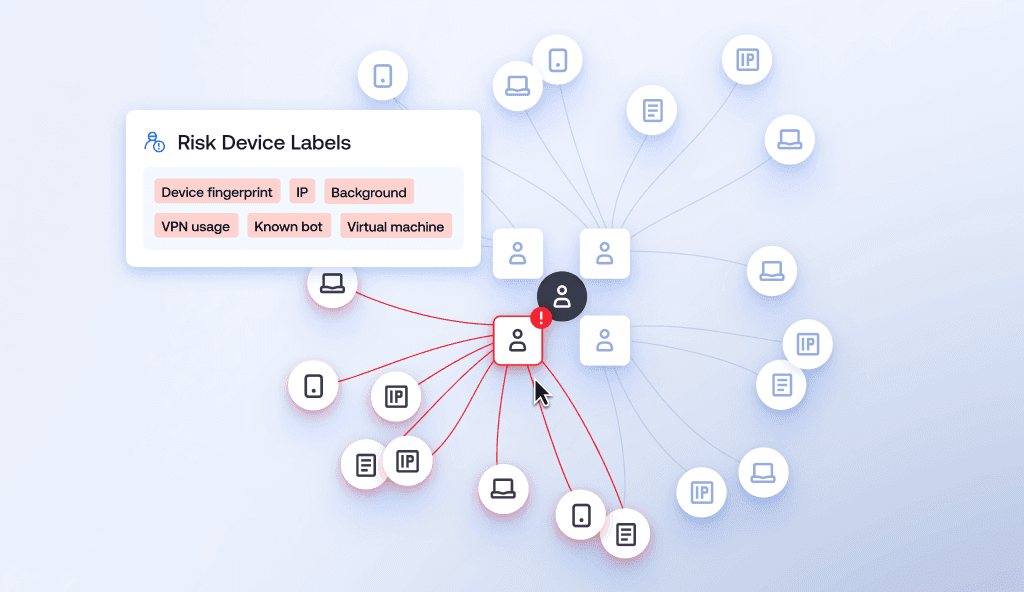
- Use of multiple KYC identities or accounts linked by the same device, IP, or behavioral fingerprint.
- Long dormancy followed by sudden activity, large withdrawals, or conversion into fiat.
- Circular trading or self-transfers across controlled wallets to simulate legitimate trading volume (wash trading).
- Payments made to third parties with no clear relationship or legitimate business justification.
The presence of one or more of these red flags doesn’t necessarily imply illicit activity. However, they do require proper due diligence and ongoing monitoring, as well as timely submission of suspicious activity reports and cooperation with law enforcement.
Key trends in crypto fraud and money laundering (2026)
Money laundering and fraud are ongoing concerns in crypto, as criminals seek to exploit the sector’s anonymity and decentralized nature for illicit purposes. Several key trends have emerged in the realm of crypto money laundering and fraud.
Trends affecting both crypto fraud and money laundering
- Using stolen and synthetic identities: Identity fraud and synthetic identity fraud occur when a fraudster opens an account for illegal activity using fake information, fabricated photos, deepfakes, pre-recorded videos, or masks to spoof identity verification systems. This can allow them to avoid being flagged as a high-risk individual by normal onboarding checks such as KYC and CDD.
- Peer-to-Peer (P2P) platforms: These enable direct transactions between users, often bypassing traditional financial institutions. While P2P platforms offer convenience and privacy, they can also be exploited for fraud or money laundering purposes.
- Ransomware: Crypto is a mainstay in ransomware attacks, with criminals demanding ransom payments in crypto to avoid detection.
- Anonymizing services: Criminals leverage anonymizing services such as VPNs, Tor networks, and encrypted messaging apps to obfuscate their identities and cover their tracks while laundering funds or committing fraud.
- Gaining access to legitimate users accounts: Scammers often use tactics such as connecting with and psychologically manipulating users on social media platforms. They can also rely on social engineering techniques, such as phishing, pretexting, and falsified human interactions to gain users’ credentials. Once fraudsters have a legitimate user’s credentials, they can access their account to carry out criminal activities, thus bypassing the normal protections that proper customer onboarding offers.
Crypto AML trends 2026
- Mixing services and tumblers: These are increasingly used to obfuscate the origin of funds by mixing them with those of other users, making it difficult to trace transactions back to their source.
- Privacy coins: Privacy-focused cryptocurrencies like Monero, Zcash, and Dash offer enhanced privacy features, making it more challenging for authorities to track transactions and identify the parties involved.
- Decentralized exchanges (DEXs): These allow users to trade cryptocurrencies without the need for a centralized authority, making it easier for criminals to exchange illicit funds with reduced risk of detection and regulation.
- Layered transactions: Criminals may employ sophisticated techniques such as layering, where multiple transactions are conducted across various wallets and exchanges to obscure the trail of illicit funds.
- Crypto ATMs: These provide a convenient way to convert cryptocurrencies into cash or vice versa. However, they can also be used to launder money with minimal KYC/AML requirements.
- Complex wallet structures: This includes multi-signature wallets and wallet clustering techniques, which enable criminals to further obfuscate the flow of funds and conceal their activities.
- Non-Fungible Tokens (NFTs): Criminals have started utilizing NFTs to launder money by transferring illicit funds through their purchase and sale.
- Money muling: Criminals frequently use third parties called money mules to transfer illicit funds. They are typically users with a clean banking history and no criminal record, allowing them to move criminal money without being noticed. Money mules are recruited through online job offers, dating sites, or darknet forums. Recruiters lure individuals by promising easy money or deceiving vulnerable populations, such as the elderly.
Crypto fraud trends
- Chargeback fraud: A very common type of fraud where scammers attempt to claim a refund using fake or stolen documents, compromised accounts, and fake identities. As crypto-to-crypto transactions can’t be refunded, chargeback fraud can only occur when fiat is exchanged for crypto via debit/credit card.
- Pump and dump: Criminals use fake news to artificially inflate the value of a particular cryptocurrency, then suddenly sell it before price crashes.
- Fraudulent ICOs: Fraudsters will promote a new crypto (or token) via an ICO, take contributions from investors, then disappear with the funds.
- Ponzi schemes: A well-established type of fraud that is frequently used by crypto fraudsters. Fraudsters take money from people, claiming to invest it into a crypto fund. Earlier investors are then paid with the money taken from new investors, giving the appearance of a return. In other words, there is no real gain, just a handover of money. This scheme ends when there is a lack of new investors or the fraud is uncovered.
Suggested read: 8 Crypto Scams to Be Aware of: A Guide for Businesses and Users
Fighting fraud in crypto in 2026
Crypto companies must take a strong, multi-layered approach to fighting fraud, especially now when a growing number of criminals are using sophisticated tactics, such as AI deepfakes, to commit crypto fraud.
Regulators increasingly expect crypto companies to have robust anti-fraud solutions as a core component of their AML and compliance frameworks, so this is something regulated businesses cannot afford to overlook. But it is not just about regulatory compliance - effective fraud prevention helps to maintain the integrity of a platform, protect customers, avoid operational losses, and safeguard a business’s reputation.
Measures crypto firms can implement to protect against fraudsters include technology such as firewalls, Extended Detection and Response (XDR) systems, and protection from Distributed Denial of Service (DDoS) attacks.
Other steps include putting in place real-time transaction monitoring to pick up red flags for crypto fraud, implementing effective Know Your Customer (KYC) and Know Your Business (KYB) procedures, and using behavioral analytics to pick up potentially fraudulent activity at an early stage. AI-driven tools are now critical for these processes as they are best able to keep up with the latest tactics from fraudsters, who themselves are regularly using AI to outwit and overwhelm more traditional anti-fraud solutions.
Crypto businesses should also educate their employees and customers to ensure they know the signs of fraud. Regular auditing and updating of key systems can also ensure continuous protection against fraudsters’ latest tools and tactics.
Suggested read: How Crypto Companies Can Avoid Scams
Global AML regulations for crypto in 2025 (+2026 outlook)
Several global and local regulations mandate that companies adopt anti-fraud mechanisms to protect the integrity of the financial system and protect consumers.
Globally, the FATF (Financial Action Task Force) Recommendations provide a benchmark for how jurisdictions should regulate to reduce risks from financial crime. These guidelines urge businesses to adopt a risk-based approach to identify and mitigate fraud. The FATF specifically calls for the continuous monitoring of transactions and customer activity to detect red flags.
AML regulations vary widely between regions and jurisdictions, with many closely following the FATF Recommendations while others diverge considerably. Understanding how different countries and regions are regulated can help to minimize risks from cross-border transactions.
Region-by-region summary of AML regulations
| Country or region | Regulation | Key effects for cryptocurrency |
| US | The Bank Secrecy Act (BSA) | Requires implementation of risk-based AML programs, imposes a duty to carry out Customer Due Diligence (CDD), requires customer screening against government lists, mandates the reporting of suspicious activity |
| The Patriot Act | Introduces a mandatory Customer Identification Programme (CIP) and enhanced due diligence requirements for correspondent accounts of foreign banks, with particular focus on international transactions and the risks of terrorism financing. Imposes criminal and financial penalties for violation of the countering the financing of terrorism (CFT) compliance regulations | |
| The Anti-Money Laundering Act (AMLA) 2020 | Broadens international information sharing rules, requires identification of beneficial ownership of companies, increases penalties for money laundering, enforces new whistleblower protections | |
| EU | 5th and 6th AML Directives (5AMLD & 6AMLD) | Extends AML obligations to CASPs, mandates public UBO registers, and enhances cooperation between FIUs. Harmonizes the money laundering offense and 22 predicate offenses, and introduces criminal liability for legal persons and individuals. |
| Transfer of Funds (TFR) Regulation (EU) 2023/1113) | Provides the Travel Rule, mandating the gathering, verifying, and sharing of specific information about the originator and beneficiary between CASPs during crypto-asset transfers, mandates various requirements, including the implementation of Enhanced Due Diligence (EDD) measures for third-country counterparty CASPs, verification of control or ownership of self-hosted wallets | |
| UK | The Money Laundering, Terrorist Financing and Transfer of Funds (Information on the Payer) Regulations 2017 | Imposes a duty to conduct AML and CTF risk assessments, mandates CDD, EDD, and Simplified Due Diligence (SDD) requirements, requires implementation of systems, policies, procedures, and controls to manage AML and CTF risksC, creates requirements for staff training and record keeping |
| The Financial Services and Markets Act 2000 (FSMA) | Sets out requirements for firms to be authorized to conduct regulated activities, makes it an offense to invite investment activity in the UK except where issued or approved by an authorized firm (with limited exemptions), mandates that people carrying out key controlling functions in a firm must be approved by the regulator | |
| Proceeds of Crime Act (PoCA) 2002 | Creates provision for confiscation and recovery of the proceeds of crime, requires regulated businesses to report suspicions of financial crime to the regulator | |
| Singapore | Payment Services Act (PS Act) 2019 | Regulates payment systems and service providersImposes licensing requirements upon payment service providers, sets out business conduct requirements for regulated firms, including AML/CTF measures |
| Payment Services (Amendment) Act 2021 | Expands and strengthens the 2019 Act | |
| UAE | Virtual Assets Regulatory Authority (VARA) guidelines and rulebook (applicable only to VASPs incorporated in Dubai) | Requires obligated entities to seek VARA approval before engaging in virtual asset activitiesImposes a duty to follow the terms of the VARA rulebooks |
| AML Rulebook of Abu Dhabi Global Market (ADGM) (applicable only to companies incorporated in Abu Dhabi) | Sets out key requirements for licensed operators, including in relation to risk assessments, CDD, sanctions compliance, and reporting obligations | |
| ADGM’s Financial Services and Markets Regulations 2015 (with amendments) (applicable only to companies incorporated in Abu Dhabi) | Create the framework for licensing, regulation, and supervision of obliged entitiesAmendments have set out key provisions, including rules for virtual assets |
Best practices for crypto AML compliance (2026)
To combat fraud, money laundering, and comply with the regulatory requirements, crypto companies should enact various best practices, including:
- Adopting Travel Rule solutions. These are systems that facilitate customer information sharing between regulated companies, empowering them to meet their duty under the FATF Travel Rule as implemented by the relevant jurisdiction/s. The Travel Rule was introduced to enhance anti-money laundering (AML) efforts and combat illicit financial activities by ensuring that relevant information about parties involved in transactions is shared between financial institutions. It aims to facilitate the tracing and monitoring of funds and improve transparency in the financial system. The Travel Rule mandates that VASPs must gather, verify, and share certain information when conducting virtual asset transfers on behalf of their clients.
- Verifying counterparties. Counterparties are the other parties to transactions involving a business’s customers, i.e., the ones sending assets to or receiving assets from those customers. These counterparties will often not be customers of the business themselves, which has traditionally presented challenges for identifying them. Understanding who these counterparties are can help crypto firms to avoid their platform being used to receive funds from, or send funds to, those involved in financial crime. Increasingly, technical solutions are helping to identify and verify counterparties, thus limiting the potential for financial crime.
- Automating risk scoring. Risk scoring is one of the most critical parts of AML compliance as it allows crypto companies to understand what level of risk for financial crime posed by a customer and/or their transactions. Customers can then receive the correct level of scrutiny to ensure any signs of financial crime are detected while avoiding expending resources on low-risk individuals and/or placing unnecessary barriers in the way of their access to financial services. Automating this process with the use of AI-powered tools can make it faster and more accurate, as well as allowing risk assessments to be dynamically updated where new information becomes available about a customer.
- Maintaining accurate audit trails. The ability to demonstrate compliance to regulators is fundamental. If businesses cannot evidence the steps they have taken to meet their regulatory duties, then this could lead to penalties and enforcement actions. Keeping accurate records enables auditors to establish whether the right processes have been followed, while also ensuring all necessary information is readily available for any investigations that must take place.
How technology enables AML in crypto
To effectively combat fraud and ensure compliance, companies need specialized tools and strategies. This is where Sumsub can play a key role in supporting fraud prevention and compliance. With our suite of KYC, KYB, and transaction monitoring solutions, we can help crypto platforms detect fraudulent activities, verify identities, and meet regulatory requirements.
Here’s how:
- Advanced KYC and KYB. Using AI to speed up customer onboarding, improve pass rates, prevent financial crime, and maintain regulatory compliance.
- Automated Transaction Monitoring. Providing AI-powered real-time, dynamic monitoring that cuts manual reviews, reduces false positives, enables faster response times, automates recordkeeping, and ensures regulatory compliance.
- Seamless Travel Rule compliance. Connecting you with more than 1,800 VASPs on widely used protocols.
- AI-driven AML screening. Checking customers and transactions against international watchlists for sanctions, adverse media, and Politically Exposed Persons (PEP).
- Regulatory Compliance. Offering a comprehensive AML and CTF solution that ensures every aspect of a business’s operations complies with the relevant regulations for its jurisdiction.
Expert view: The future of AML in crypto
Crypto Report 2025: The Tipping Point
Explore fresh industry data, rising fraud threats, and evolving regulations, along with expert recommendations to guide your strategy: Crypto Report
FAQ
-
What is AML in crypto?
AML in crypto refers to anti-money laundering processes for businesses dealing with cryptocurrencies and other virtual assets. It involves the regulatory requirements with which obliged entities must comply as part of their legal duty to prevent money laundering activity on their platforms.
-
How does AML apply to cryptocurrency exchanges?
Cryptocurrency exchanges will have regulatory AML obligations. Exactly what these obligations are will depend on the jurisdiction in which the exchange is incorporated, but typically, they will include things like carrying out risk assessments on customers, completing KYC and KYB processes to confirm who customers are and what their level of risk might be, ongoing monitoring of transactions, recordkeeping, and reporting of any suspicious activity. Crypto exchanges will also need to gather, verify, and share relevant information when conducting virtual asset transfers on behalf of their clients.
-
What is the Travel Rule in crypto?
The Travel Rule was introduced by the Financial Action Task Force (FATF). It sets international standards for customer information sharing between firms to facilitate more effective action on AML, CTF, and the prevention of other forms of financial crime. The rule has been implemented by various jurisdictions and applies to all regulated financial institutions, including Virtual Asset Service Providers (VASPs).
-
How can crypto businesses stay AML compliant?
To maintain AML compliance, crypto businesses must ensure they understand their regulatory obligations, then take appropriate steps to meet those obligations. Typically, this will involve measures such as creating effective AML frameworks and procedures, taking a risk-based approach to customer onboarding and monitoring, appointing a Money Laundering Reporting Officer, training staff, carrying out effective KYC and KYB processes, transaction monitoring, recordkeeping, and reporting suspicious activity. It will also include gathering, verifying, and sharing information in line with Travel Rule obligations.
-
What tools help detect money laundering in crypto?
There are various AML tools that can help crypto firms meet their regulatory obligations. These include AI-enhanced KYC and KYB tools, automated transaction monitoring software, and integrated AML solutions that cover all aspects of a business’s AML framework.
Relevant articles
- Article
- 3 weeks ago
- 9 min read

- Article
- 5 days ago
- 12 min read
Learn how device intelligence assesses device risk in real time using technical signals and device fingerprinting—without disrupting the customer exp…
What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.