- May 13, 2026
- 12 min read
What Is Device Intelligence and How Does It Stop Fraud?
Learn how device intelligence assesses device risk in real time using technical signals and device fingerprinting—without disrupting the customer experience.
Fraud is industrializing like never before. Sophisticated fraud nearly tripled from 2024 to 2025, with multi-step attacks rising from 10% to 28% of all identity fraud, representing a 180% YoY increase.
Fraud-as-a-service tools, meanwhile, have become cheap and easily accessible, allowing bad actors to cause havoc with huge fraud campaigns that would have been unimaginable just a few years ago. With just $1,000, fraudsters can inflict losses of up to $2,500,000 within a single month.
This makes it easier for criminals to mass-test username and password combinations bought from the dark web in account takeover attacks, with adaptive bots designed to learn and become better with time. Recent studies suggest this is a huge issue. The FBI says bank account takeover fraud resulted in over $262 million in reported losses in 2025, while Sumsub’s most recent Identity Fraud Report found that account takeover fraud was the second-most common type of third-party fraud.
Thankfully, fraud prevention is evolving just as quickly. One of the most effective tools for combating this unprecedented rise in fraud is device intelligence.
Device intelligence builds a dynamic picture of how a user interacts with a platform. It uses device fingerprinting, behavioral signals, and AI-driven analysis to identify suspicious activity without adding friction for genuine users. Let’s dive into the details.
What is device intelligence?
Device intelligence is a comprehensive process of collecting and analyzing data about a device’s hardware, software, and network. This intelligence then helps businesses make more informed decisions, such as whether to limit a user’s activity to prevent suspected fraud.
These signals have long been used in advertising and analytics, but they are also a core component of fraud detection, helping identify suspicious devices, link related activity across accounts, and detect threats.
When a device connects to a website, it shares data in the background that the user does not see. These include browser type, operating system, IP address, screen resolution, installed fonts, and network configuration. On top of this, behavioral signals like mouse movements, interaction speed, and even touch pressure can add further context.
When this vast amount of data is combined, these signals form a unique, holistic device profile that can tell one device from another, helping to distinguish a legitimate user from an account takeover attack.
This information is invaluable for securing digital trust as traditional identifiers become increasingly unreliable on their own for detecting fraud.
Suggested read: Fraud Detection and Prevention—Best Practices
Which fraud risks can device intelligence detect?
Breakthroughs like advanced deepfake technology have made it easier for fraudsters to appear legitimate on the surface. Thankfully, signals from a device, its network, and its environment can provide intelligence that effectively helps identify several common fraud risks, including:
Account takeover attacks
Device intelligence can detect when valid credentials are being used from an unfamiliar device, unusual location, or suspicious network.
Credential stuffing and bot attacks
Device intelligence can help identify automated login attempts through device and browser inconsistencies, as well as interaction patterns that do not match normal user activity.
Synthetic identity fraud
Device intelligence can flag newly created accounts with an inconsistent signal or no trusted device history.
Emulator and spoofed environments
Device intelligence can detect rooted or jailbroken devices, virtual machines, emulators, headless browsers, and manipulated operating systems that may be used to hide a user’s true environment.
Multi-accounting and fraud rings
Shared device and network signals can help link accounts that appear separate but are actually controlled by the same person or group.
Attempts to bypass verification with deepfakes
Device intelligence does not determine whether a person or document is real or fake. Instead, it analyzes the context around the verification attempt. For example, even if a synthetic identity or deepfake were to pass a liveness check, device intelligence could still flag its context as suspicious, such as the use of an emulator, rooted device, spoofed environment, new device with no prior reputation, unnatural navigation or typing patterns, VPN or proxy use, or a mismatch between device, IP, and geolocation signals.
How device intelligence works
Device intelligence operates as a layered fraud detection system that collects device data, analyzes it in context, and assigns a risk score in real-time. This makes real-time fraud detection possible without inconveniencing legitimate users.
The process starts with gathering device signals that are then combined into a device fingerprint. This fingerprint is compared against historical activity, known fraud patterns, and behavioral baselines to determine whether an interaction is legitimate.
If the signals match expected behavior, the user can proceed seamlessly. However, fraud-detection systems can trigger extra verification, limit activity, or block sessions if there are signs of automation or a mismatch between known credentials and a device.
Data collection: Device signals explained
Device intelligence collects a range of signals associated with the user’s device and session. These include technical attributes and behavioral data.
Technical signals that help create the structural foundation of a device fingerprint include:
- Browser type
- Operating system
- IP address
- Screen resolution
- Installed fonts
- Network configuration
- Device type and model
- VPN provider
- Browser automation detection
- Whether incognito mode is used
Behavioral analytics can add a dynamic layer of insight through capturing how users interact with a platform in real time. These signals include:
- Typing speed and keystroke patterns
- Mouse movements and cursor trajectories
- Swipe patterns and touch interactions
By analyzing these interaction patterns, systems can build a behavioral profile of each user over time. Because these patterns are difficult to replicate consistently, they are highly effective at distinguishing genuine users from bots, fraudsters, and account-takeover attempts.
This is also where bot detection is useful. Today’s bots are becoming better at mimicking some human interaction patterns, including realistic pauses and interaction speeds, but they are harder to disguise at scale. Automated tools may still leave clues that suggest involvement in a wider fraud network, such as repeated device and browser configurations, headless browser signals, VPN use, or connections to devices and IP addresses already associated with suspicious activity.
Combining these many, many signals, device intelligence systems can build a reliable picture of whether an interaction is genuine or potentially fraudulent.
Key technologies powering device intelligence
Device intelligence relies on a combination of technologies that work together to identify risks and enable real-time fraud detection. These systems analyze device-level signals—such as rooted or emulated environments, network anomalies, and fingerprint inconsistencies—alongside machine learning–based security, bot detection, and edge computing to build a comprehensive picture of each interaction. User behavior signals can be incorporated as an additional layer to strengthen detection.
Device fingerprinting
Device fingerprinting is the foundation of device intelligence. This is a process of building a unique “device fingerprint” by combining multiple characteristics associated with a device in a holistic profile.
While none of the identifiers are unique on their own, such as browser type and screen resolution, together they form a profile that can reliably distinguish one device from another.
Unlike cookies, which can be deleted, or IP addresses, which can be masked, a fingerprint device profile allows fraud detection systems to recognize returning devices, flag unknown ones, and identify inconsistencies.
Machine learning and AI
Machine learning models are used in fraud detection to analyze device data at scale and identify patterns that would be impossible to detect manually. Machine learning allows fraud detection systems to adapt continuously and improve accuracy as new threats emerge.
These models are trained on large volumes of historical interactions, learning what “normal” behavior looks like for different users, devices, and contexts. When a new activity deviates from these patterns, such as unusual login times, it can be flagged instantly.
Behavioral analytics and monitoring
Behavioral analytics adds an extra layer of context to device intelligence through analysis of how users interact with a platform. While device intelligence focuses on the device, network, and technical environment, behavioral monitoring evaluates key platform events such as logins, sign-ups, password updates, settings changes, address changes, and verification sessions.
This information helps build a live behavioral profile for each user and continuously updates their risk score. For example, even if a login attempt uses the correct credentials, it may nonetheless appear suspicious if it comes from a new device or is immediately followed by a password change.
Behavioral monitoring can also help support automated fraud-prevention. When risk exceeds a set threshold, businesses can trigger additional checks, send the case for manual review, request stronger authentication, such as a liveness check, or block the activity before risk escalates.
This information helps provide a holistic picture of user risk.
Big data analytics and edge computing
Fraud detection systems aggregate signals from large volumes of interactions to identify patterns, detect anomalies, and continuously refine risk models. As a result, the effectiveness of device intelligence depends on the ability to process high volumes of device-level data—such as environment, network, and fingerprint signals—in real time, with user behavior serving as an additional layer.
Edge computing security allows this analysis to happen closer to the point of user interaction, which reduces latency and supports real-time fraud detection, allowing decisions to be made in milliseconds.
The result is a system that can scale across high volumes of traffic while still responding instantly to suspicious activity.
Contextual awareness
Device intelligence also incorporates contextual awareness to help understand the broader circumstances surrounding an interaction.
This includes factors such as location, time of access, and transaction history. When this context is layered on top of device data, fraud prevention systems can improve account takeover detection rates and strengthen fraud detection, particularly in high-risk sectors such as banking.
Suggested read: What is Device Fingerprinting?
Device intelligence vs device fingerprinting
Device fingerprinting and device intelligence are sometimes confused.
❗ Device fingerprinting answers the question of what the device is, while device intelligence answers how risky the device is.
Device fingerprinting focuses on identifying a device using signals such as browser type and version, operating system, device model, screen size, language settings, time zone, and other configuration details. This allows platforms to recognize returning devices, flag unfamiliar ones, and detect inconsistencies when device characteristics change unexpectedly.
Device intelligence goes a step further and evaluates the risk associated with a device and its activity in context. It considers not just what the device is, but also how and where it is used. For example, it can reveal whether the same device appears across multiple accounts, has been linked to previous fraud, is used after account takeover attempts, is associated with repeated failed payments, or operates through suspicious network infrastructure.
Real-world use cases by industry
Device intelligence is valuable across industries where fraudsters target accounts, payments, payouts, subscriptions, and onboarding flows. Its ability to help businesses assess device risk across the user journey and respond when the device, network, or usage pattern suggests suspicious activity makes it essential across a range of industries:
E-commerce: Device intelligence helps merchants assess the device behind a purchase, not just the payment details. It can flag risky signals such as repeated failed payment attempts from the same device, use of emulators or proxies, unusual device velocity, or a device previously linked to chargebacks or account abuse. This helps merchants detect card testing, fake accounts, refund abuse, and suspicious checkout behavior earlier, while allowing trusted returning customers to complete purchases with less friction.
Banking and fintech: In banking, device intelligence can help detect account takeover, payment fraud, and unauthorized access by identifying when a login, password reset, account change, or transfer request comes from a new, risky, or manipulated device. For example, if a customer logs in with valid credentials from an unfamiliar device using a proxy, shortly after a password reset, and then tries to add a new beneficiary or move funds, device intelligence can raise the risk level and trigger step-up verification or manual review before money leaves the account.
Telecommunications: Telecom providers can use device intelligence to help detect SIM swap fraud, account takeovers, and subscription abuse. A request to change account details, transfer a number, or activate a new SIM may carry a higher risk if it comes from a new device, a manipulated environment, a suspicious IP address, or a device already linked to previous abuse.
Digital services and SaaS platforms: Device intelligence can help protect user accounts and detect automated abuse at scale. It can identify suspicious sign-up patterns, account sharing, credential stuffing, bot-driven activity, or the use of a single device to create or control multiple accounts.
Crypto: Crypto platforms can use device intelligence to detect suspicious logins, wallet access anomalies, payout abuse, and coordinated fraud activity. A new device, proxy connection, emulator, or sudden device change before a withdrawal request can indicate elevated risk, even if the user’s credentials or identity data appear valid.
iGaming: In iGaming, device intelligence helps detect when one person or group is operating multiple accounts to abuse bonuses, bypass restrictions, or automate play. Signals such as repeated devices across accounts, emulators, VPN or proxy use, device farms, unusual signup velocity, or device links between deposits and withdrawals can help identify bonus abuse, multi-accounting, bot-driven activity, and self-exclusion evasion. This allows platforms to restrict suspicious bonuses, trigger verification, or review high-risk withdrawals without adding unnecessary friction for legitimate players.
For example, Anakatech, a B2B iGaming technology provider, uses Sumsub’s Device Intelligence to identify high-risk users early in the journey and detect fraud signals such as multi-accounting without adding extra friction for legitimate players.
Monika Gincheva, Head of Risk, Payments and Operational Compliance at Anakatech Group, said:
Device Intelligence has fundamentally improved our approach against fraudsters. Instead of adding friction for everyone, we now silently identify high-risk players at early stages. Focusing on the device rather than just the identity has allowed us to cut multi-accounting fraud significantly while keeping the user journey seamless.
Device intelligence vs legacy security tools
Legacy security tools were built around static identifiers like passwords, security questions, and one-time passwords. While these are still useful for keeping accounts safe, they are increasingly ineffective on their own against modern threats.
Credentials can be stolen and reused through credential stuffing, IP addresses can be masked using VPNs, and multi-factor authentication can be bypassed through social engineering.
Device intelligence adds an extra layer of security with signals that are harder to manipulate consistently, providing the full context of an interaction and helping fraud detection systems be more proactive.
Suggested read: Bypassing Facial Recognition—How to Detect Deepfakes and Other Fraud
Benefits of device intelligence for fraud detection
Device intelligence strengthens fraud prevention, helping businesses assess risk continuously across the user journey, from signup and login to transactions, payouts, refunds, and account changes.
One of its main benefits is earlier risk detection. Device signals can help identify suspicious patterns before fraud turns into financial loss. For example, a new device appearing just before a payout change, one device creating multiple accounts, or an emulator being used during signup can all indicate elevated risk.
Device intelligence also helps teams make more accurate decisions. Instead of relying only on user-submitted data or payment details, fraud teams can evaluate device context, network signals, device integrity, velocity, and historical reputation. This helps distinguish trusted users from attackers, even when fraudsters use valid credentials or stolen identity data.
Another benefit is targeted friction. Trusted users can continue with fewer interruptions, while risky users can be stepped up, reviewed, delayed, limited, or blocked. This helps protect conversion while still reducing fraud exposure.
Device intelligence also supports scalable fraud operations. As fraud becomes increasingly automated through bots, device farms, emulators, and coordinated account networks, device-level signals help teams detect recurring patterns across large volumes of interactions without relying solely on manual review.
Reducing false positives and customer friction
A major challenge in fraud prevention is balancing security with user experience. Overly strict systems can generate high levels of false positives of fraud, blocking legitimate users or forcing unnecessary verification steps that result in high drop-off rates and lost conversions.
Device intelligence helps reduce this because it provides additional context. Instead of flagging activity based on a single risk factor, it evaluates whether the overall behavior makes sense. For example, a login from a new device may still be accepted if interaction patterns, session behavior, and historical context align with the user’s profile.
This leads to more accurate decisions with fewer disruptions. Legitimate users can proceed unaffected, while genuinely suspicious activity is acted upon more effectively.
This improves both conversion and retention. Customers are less likely to abandon transactions or accounts due to frustration with friction, while fraud detection solutions and tools operate in the background, maintaining higher security levels.
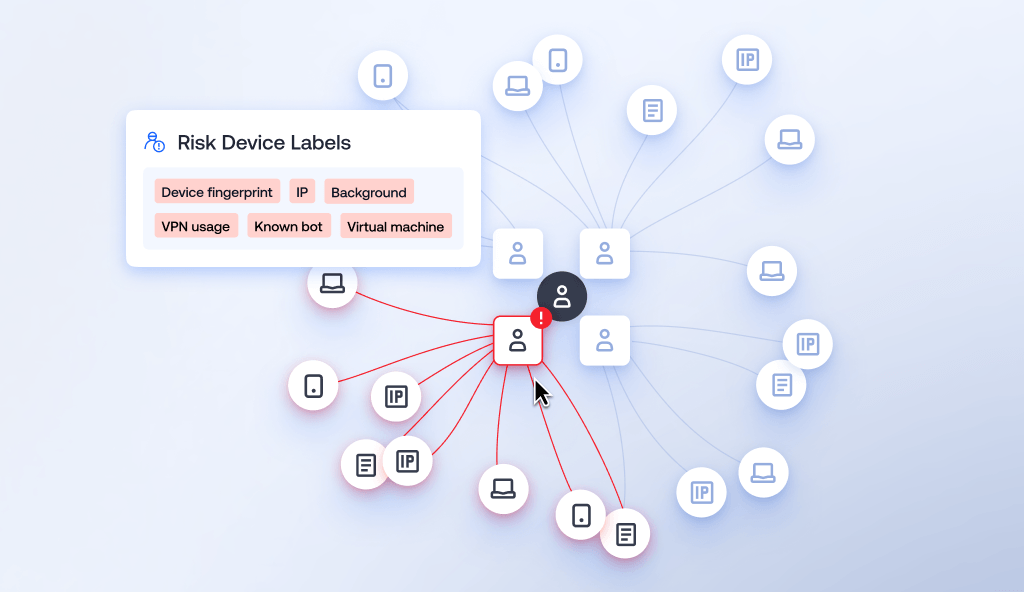
Device and network intelligence with link analysis
Device intelligence is more powerful when combined with network intelligence, which helps understand how interactions are connected across a wider ecosystem.
While a single device profile can highlight suspicious behavior, attackers often operate in sophisticated clusters, using multiple accounts, shared infrastructure, and automated tools.
Mapping these relationships reveals patterns that would otherwise remain hidden.
Visual link analysis can reveal how devices, users, IP addresses, and sessions are linked, helping investigators and automated systems identify coordinated fraud activity.
Data collection: Device and network signals
In addition to standard device signals, network intelligence incorporates data about how devices interact within a wider environment.
This includes shared IP addresses, proxy or VPN usage, session timing patterns, and links between multiple accounts accessing a platform. For example, dozens of accounts logging in from slightly different devices but the same network infrastructure may indicate coordinated activity.
As automated attacks like credential stuffing become more accessible, bot detection can play a key role in fraud prevention. Automated attacks often leave network-level traces, like synchronized actions or traffic patterns that differ from human behavior.
Combining device-level and network-level signals, fraud detection systems can identify coordinated campaigns and keep users safe.
Connecting the dots with visual link analysis
Once signals are collected, visual link analysis helps make sense of them by mapping relationships between entities.
This connects devices, accounts, IP addresses, and behaviors into a network graph, making patterns easier to identify. This can reveal multiple accounts linked to the same device fingerprint or a cluster of devices sharing infrastructure commonly associated with fraud.
This is particularly valuable for detecting complex threats such as account takeover rings, multi-accounting, bot-driven attacks, and mule networks, helping analysts more easily explore how different elements are connected and identify the root of fraudulent activity.
Combining network intelligence with visual link analysis allows businesses to adopt a more holistic view of fraud that can detect fraud as it happens while exposing the automated threats and industrialized criminal networks behind them.
Suggested read: What Is Fraud Scoring? A Guide for Businesses
Why device intelligence is essential today
In 2026, we are in the midst of an AI-fueled fraud crisis, where advances in technology have made fraud more scalable, sophisticated, and difficult to detect with traditional controls alone. Credential-stuffing tools, bulk-stolen login details, synthetic identities, spoofed environments, and AI-assisted impersonation can all make risky activity appear legitimate on the surface.
Identity itself has also become less reliable as a signal. Stolen credentials may be reused across services, while synthetic identity fraud can combine real and fake information to create accounts that pass basic verification checks. An identity may appear legitimate on the surface, even when it is not tied to a real human and is being used to facilitate crime.
This is where device intelligence becomes essential. Instead of relying only on what the user claims, device intelligence focuses on how the account is accessed and operated. It can help assess whether a device is trusted or new, whether the environment has been manipulated, whether the device is linked to prior abuse, whether a single device is being used across multiple accounts, and whether the timing or pattern of activity suggests automation or coordination.
Device intelligence is particularly effective at identifying sophisticated fraud attempts involving spoofed or emulated devices, rooted or jailbroken devices, incognito or privacy modes, VPNs, proxies, location spoofing, and other suspicious device or network conditions. These signals are harder to rotate or fake consistently at scale, especially when they are combined over time and across events.
It also strengthens fraud detection at critical moments, such as login, payment, payout, and account changes, where risk is often highest. A new or suspicious device at these stages can indicate account takeover, payment fraud, or payout abuse, even when credentials and identity data appear valid.
As fraud becomes more dynamic, static checks and one-time verification are not enough. Device intelligence adds a continuous risk layer across the user lifecycle, helping businesses detect risk earlier, apply controls at the right moment, reduce reliance on manual review, and maintain a better balance between security and user experience.
Its value is not just in detecting individual suspicious events, but in understanding patterns across devices, sessions, and accounts, making fraud harder to scale and easier to contain.
Device Intelligence FAQ
-
What is device intelligence in fraud prevention?
Device intelligence uses device-level data in fraud prevention to assess whether an interaction is legitimate. In simple terms, it focuses on analyzing the device’s environment and activity, such as network signals, integrity, and fingerprint consistency, to detect risk, rather than relying solely on what the user claims.
-
How does device fingerprinting work?
Device fingerprinting works through the collection of technical characteristics, such as browser type, operating system, and screen settings, to create a unique profile. It helps identify suspicious activity and distinguish real users from attackers in fraud detection.
-
How does device intelligence stop account takeover?
Device intelligence helps prevent account takeover fraud by detecting mismatches between behavior and device profiles. This enables faster account takeover detection and stronger account takeover prevention when attackers use stolen login credentials.
-
Is device intelligence effective against AI-driven fraud?
Yes. Modern fraud detection systems use AI and machine learning to analyze device-level signals at scale, enabling real-time risk assessment. This makes AI-driven fraud detection more adaptive, helping businesses identify automated and AI-driven attacks as they occur, with user behavior incorporated as an additional signal.
Relevant articles
- Article
- Yesterday
- 10 min read
Discover how fraudsters attack facial recognition with deepfakes and spoofing, and how liveness detection helps stop biometric attacks.
- Article
- Apr 1, 2026
- 18 min read

What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.


