- Sep 23, 2025
- 7 min read
What Is Chargeback Fraud and How to Prevent It in 2025
Are you struggling to stop false transaction claims? Here you’ll find several ways to stop them and free your business of fraud.

Chargebacks cost money twice: you lose the sale and then pay in fees, ops time, and higher processing risk. It can also lead to lost shipping, additional transaction processing costs, and reputational damage.
And not just that—when ratios rise, card brands can place you in monitoring programs and, in severe cases, acquirers may add you to Mastercard MATCH (formerly TMF), making future processing difficult. In this guide, you can read about what chargeback fraud is, how disputes actually flow, and which controls truly reduce losses.
What is chargeback fraud?
Chargeback fraud (first-party fraud) is when a customer purposefully lies about the status of a purchase. This is typically done with the sole intention of getting a refund and keeping the item. Customers may falsely claim that they’ve never received the order or never even authorized the transaction. There is also true (third-party) fraud in chargebacks—when an unauthorized person uses the cardholder’s details.
Imagine someone buys a new laptop online using a credit card. After receiving it, they claim to the bank that they never got the laptop and request a refund. The bank reverses the payment, so the buyer keeps both the laptop and the money.
Common types of chargeback fraud
Since not all chargebacks happen for the same reason, it’s important to understand the different types. Recognizing the root cause helps businesses choose the right prevention and response strategy.
Not every chargeback should be considered fraud, however. Card networks group disputes into fraud, authorization/processing errors, and consumer disputes (like defective/undelivered goods, or confusing descriptors).
Merchant error is not fraud and should be fixed at the root—fulfillment, customer service, and billing descriptors—not by “more fraud tools.” Let’s dive into different types of chargebacks and what they bring about.
| Type of chargeback | Who initiates it | Description | Merchant vs. bank |
| Friendly (first-party) fraud | Cardholder (first-party)(intentional or accidental) | Customer disputes a legitimate purchase, often claiming it wasn’t authorized, or they didn’t receive the item, even if they did | Outcomes depend on the evidence and on Visa/Mastercard rules. With the right evidence, merchants do recover a meaningful share of disputes |
| Criminal fraud (true third-party fraud) | Fraudster (third-party) | For example, a criminal uses stolen card info to make unauthorized purchases | A cardholder; merchants can dispute with strong proof |
| Merchant error | Merchant | Mistakes like mis-ships, duplicate charges, wrong or defective products, or service not delivered | Entirely preventable; merchants found liable, it's best to correct the root cause |
How does a chargeback work?
A chargeback follows a clear process between the customer, their bank, and the merchant. Here’s how it works:
- Purchase: The customer buys goods or services using their debit or credit card.
- Dispute: The customer contacts their issuing bank to dispute the charge, claiming fraud, error, or dissatisfaction. The bank assigns the dispute a “reason code,” which determines what evidence the merchant must provide to fight it.
- Bank review: The issuing bank reviews the claim and may issue a provisional credit to the customer.
- Merchant notification: The merchant receives a chargeback notice with details of the dispute.
- Merchant response (representment): The merchant can respond by submitting evidence (such as receipts, delivery confirmation, or logs) to contest the chargeback. This stage is often referred to as “representment” or “second presentment” in card-network rules. Importantly, merchants face strict deadlines—typically 30–45 days depending on the network. Missing these deadlines usually means an automatic loss, no matter how strong the evidence.
- Bank decision: The issuing bank (and sometimes the card network) evaluates the evidence and makes a final ruling. If the bank rules against the merchant, some networks allow escalation through pre-arbitration or even arbitration, though these steps are less common and can be costly.
- Outcome: If the bank sides with the customer, the funds are permanently taken from the merchant. If the merchant wins, the chargeback is reversed. When they submit strong documentation, merchants win around 50% of representation cases.
Can chargebacks be illegal?
No, if it’s a legitimate dispute.
Legitimate disputes are protected by consumer law (for example, the US Fair Credit Billing Act). Knowingly filing a false dispute can be treated as fraud or theft. Penalties depend on the country/state and on the facts.
Yes, if the cardholder knowingly abuses the process.
When someone intentionally disputes a valid charge—say, after receiving the item in good condition—this is considered chargeback fraud, a deceptive act that can be treated as theft or fraud.
This misuse can lead to legal consequences, including:
- Criminal offense, such as theft, credit card fraud, wire fraud, or mail fraud, especially if the conduct crosses state or federal lines.
- Prison sentences or fines. Many states impose 1 to 3 years of imprisonment for fraudulent chargebacks, with penalties ranging from thousands to tens of thousands of dollars. Severe or large-scale fraud can mean even harsher penalties.
Some industries face a higher risk due to the nature of their transactions. For example, travel and hospitality see the highest average chargeback amounts (~$120), followed by digital goods and subscriptions. The most prevalent industries are:
- E-commerce retailers. High transaction volumes and card-not-present sales make online shops frequent targets.
- Ticket platforms. Digital ticketing is prone to friendly fraud and abuse, often linked to resale activity, digital delivery, and cancellation disputes.
- Subscription services. Customers sometimes deny recurring charges they forgot to cancel.
- Travel and hospitality. Cancellations, no-shows, and disputes over services delivered drive frequent chargebacks.
Impact of chargebacks on businesses
Chargeback claims have a substantially negative effect on businesses. The average chargeback amount increased to $169.13 in 2024, compared to $165 in 2023. In 2025, businesses globally are expected to lose $15 billion to fraudulent chargebacks, with chargeback volume climbing from $33.79 billion in 2025 to an estimated $41.69 billion by 2028, according to a study by Datos Insights.
Even small businesses see this firsthand: one family-owned butcher store lost over $500 when an order was fulfilled and then overturned with a chargeback.
Chargebacks can impact businesses in multiple ways.
- Revenue loss. Every chargeback directly reverses a sale, stripping away not only the transaction value but also the associated profit. Over time, repeated disputes can lead to great revenue loss.
- Operational costs. Beyond the refund itself, merchants often face extra fees from payment processors, along with the time and resources required to collect evidence, respond to disputes, and manage internal workflows.
- Merchant account risk. A high chargeback ratio signals risk to banks and payment processors. This can lead to higher processing fees, stricter monitoring, account termination, or even being added to the Mastercard MATCH.
- High ratios: High dispute ratios can trigger monitoring programs run by Visa and Mastercard, with escalating fees if you stay above thresholds.
Chargeback claims can also lead to reputational damage. If payment processors notice an overwhelming chargeback ratio, they may limit the merchant’s monthly volume of payments, terminate their account entirely, or place them in a Mastercard MATCH, which designates them as an above-average risk customer. Once placed in a Mastercard Match, the merchant may have no choice but to use a “high-risk” payment processor, or even create a new legal entity to restart their business.
Suggested read: Fraud Detection and Prevention—Best Practices for 2025
How to prevent chargeback fraud
Because about 45% of merchants’ chargebacks are fraudulent, prevention tools are more important than ever. However, tools are not the only way to protect your business—here are some essential tips to fight back against chargeback fraud.
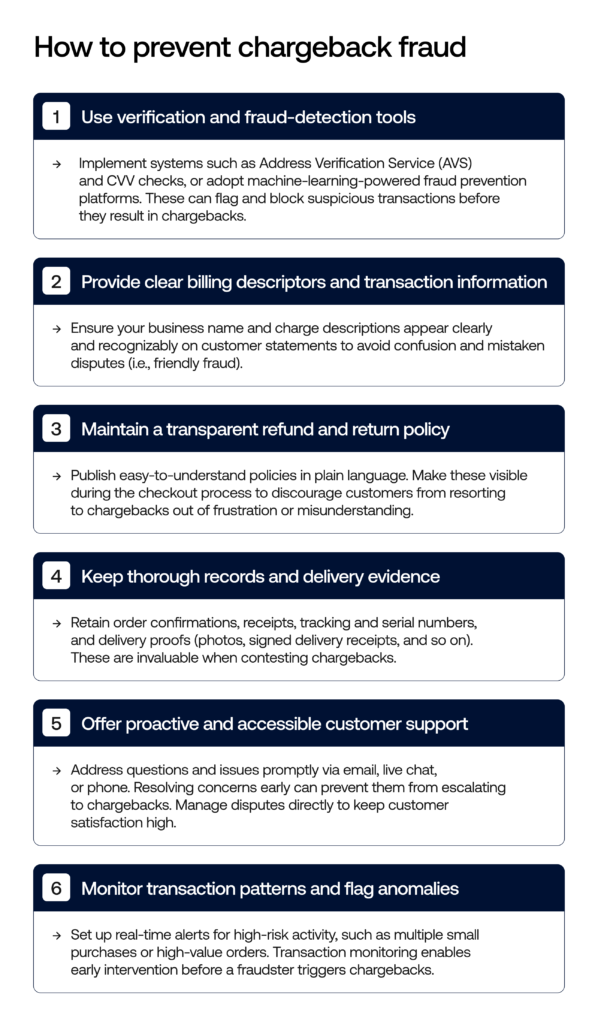
If you want to be extra safe, you can implement these additional methods of preventing chargeback fraud:
- 3D Secure (EMV 3DS): Use this feature on risky orders to shift liability in fraud disputes when eligible, while keeping checkout simple for trustworthy customers.
- Visa Compelling Evidence 3.0: Provide standard historical signals using Order Insight/VROL to prevent first-party disputes, whether before or after they are made.
- Issuer–merchant collaboration: Share digital receipts and detailed order information through established channels so customers can easily recognize charges in their banking apps.
- Clarity and operations: Use a clear billing description, include order details in receipts, make refund and return terms easy to find, and offer quick access to customer support.
- Risk-based screening: Combine AVS/CVV with device and behavior checks, use rules for suspicious activity, and verify order locations. When possible, require a signature or ID for high-value deliveries.
Suggested read: Payment Fraud Protection: Use Cases
What to do when you get a chargeback
If your business receives a chargeback, follow these steps to respond effectively:
- Work on the reason code. Build evidence that matches the network’s criteria (don’t argue “narratives”, match the rule).
- Use the right artifacts. For CNP fraud, rely on 3DS results or CE3.0-qualifying history; for non-fraud disputes, provide delivery proof, service logs, and clear policy disclosures.
- Be selective with escalation. Pre-arbitration/arbitration is expensive, so escalation should occur only when your packet meets the “compelling evidence” standard.
- Tighten the feedback loops. Fix the process that produced the dispute (descriptor, fulfillment, comms) so the same pattern doesn’t repeat.
Chargeback fraud detection tools
Businesses don’t have to face chargeback fraud alone—specialized platforms like Sumsub provide advanced detection capabilities that identify high-risk activity before it turns into disputes. These tools combine AI, behavioral analytics, and real-time data to stop fraudsters in their tracks. Two-thirds of respondents in the merchant survey are being smart with their business tactics—they are either already using AI-powered fraud prevention tools or plan to do so in the future.
Here are some of the key things these platforms can detect:
- Suspicious transaction patterns. Spotting unusual order behavior, such as multiple rapid purchases or mismatched billing and shipping details.
- Repeat abusers. Identifying customers who file frequent disputes or exploit return/refund loopholes.
- Device intelligence. Linking users and transactions to unique device characteristics to detect multiple disputes and refunds from the same device, identify device masking, and uncover spoofed or compromised devices.
- Velocity checks. Flagging unusually high purchase frequency, order volume, or value in a short time frame.
- Geolocation mismatches. Detecting when a user’s IP, billing address, and delivery location don’t align.
- Behavioral biometrics. Analyzing how users type, swipe, or navigate to distinguish genuine customers from bots or fraudsters.
- Account takeover indicators. Monitoring sudden changes in login behavior, password resets, or unusual account activity.
Sumsub’s approach to chargeback prevention
Sumsub employs a sophisticated, real-time, multi-layered strategy, anchored by pre-KYC fraud signal detection, to stop fraud before it results in chargebacks. With the help of Fraud Prevention solution, businesses can block fraudulent activity at any payment stage, reduce disputes, and keep their revenue safe without adding friction to genuine customers.
Here are some key components of Sumsub’s fraud detection tool:
Real-time fraud scoring
Sumsub evaluates each transaction or interaction using dynamic, AI-powered risk scoring, pre-KYC. Fraud Management includes device intelligence, behavior patterns, and historical risk signals to assign a fraud score to help businesses act immediately (approve, verify, hold, or block).
Behavioral data analysis across the user journey
Rather than focusing only on onboarding, Sumsub continuously monitors behavioral analytics, such as typing, navigation, mouse movements, login attempts, and transaction anomalies, to detect deviations from normal user patterns. This ongoing profiling helps catch malicious behavior before a chargeback happens.
Device fingerprinting and intelligence
Sumsub uses detailed device information—like settings, browser identification, and smart signals such as incognito mode and proxy usage—to identify fake devices and unusual activity. This helps detect threats in real time during every step of the user interaction, among which are multiple disputes from one device, device masking, and other suspicious device activity.
AI-driven network analysis
The Fraud Network Detection tool identifies hidden links between users, even across different accounts. This helps find repeat offenders, groups of related accounts, or organized fraud operations, such as multi-accounting or bot farms, before any fraud occurs.
Data orchestration with AI-powered monitoring
Sumsub collects and analyzes data from different sources, such as devices, user behavior, and KYC/AML signals, in real time. This process creates risk scores and triggers automatic responses. This approach helps reduce manual work while keeping detection accurate.
Identity verification
Liveness, face authentication, and document verification can be used to ensure that one account is linked to one person, collect applicant data, collect evidence that the transaction was made by the account holder to dispute friendly fraud, and use dynamic friction on high-risk transactions.
FAQ
-
What is chargeback fraud?
Chargeback fraud occurs when a customer disputes a legitimate transaction to get their money back while keeping the goods or services.
-
Is a chargeback considered fraud?
Not always—chargebacks can be valid, but if a buyer knowingly disputes a legitimate charge, it becomes fraud.
-
What are examples of chargeback fraud?
Examples include “friendly fraud” (denying a purchase they made) and third-party fraud, which involves using stolen card details or exploiting merchant errors.
-
How do you prevent chargeback fraud?
Merchants can use fraud detection tools, clear billing descriptors, and strong transaction records to minimize disputes.
-
What happens if a chargeback is fraudulent?
If proven, merchants can challenge it with strong documentation, and the card issuer may reverse the refund, but results vary by industry, bank, and the quality of proof.
-
Is chargeback fraud a crime?
It can be a crime if the person knowingly files a false dispute. Legitimate disputes remain lawful.
Relevant articles
What is Sumsub anyway?
Not everyone loves compliance—but we do. Sumsub helps businesses verify users, prevent fraud, and meet regulatory requirements anywhere in the world, without compromises. From neobanks to mobility apps, we make sure honest users get in, and bad actors stay out.